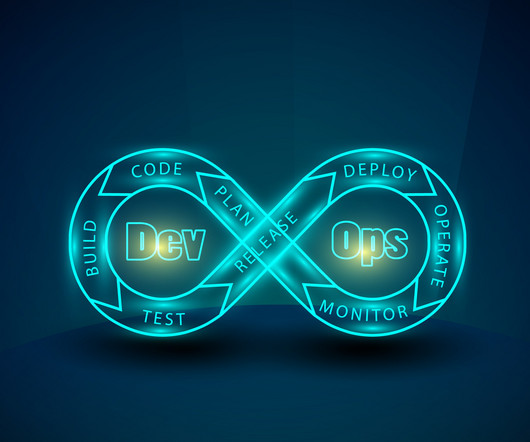
Why Transparency and Trust Should Underscore DevOps
SecureWorld News
OCTOBER 25, 2024
The dynamic and ever-evolving world of DevOps requires businesses to deliver high-quality software, under pressure, at an accelerated pace. As cybersecurity concerns continue to grow, many organizations are also now embracing DevSecOps, integrating many security practices throughout the DevOps process.





















Let's personalize your content