Atomic Stealer Distributes Malware to Macs Through False Browser Downloads
Tech Republic Security
NOVEMBER 22, 2023
Atomic Stealer malware advertises itself through ClearFake browser updates disguised as Google's Chrome and Apple’s Safari.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Tech Republic Security
NOVEMBER 22, 2023
Atomic Stealer malware advertises itself through ClearFake browser updates disguised as Google's Chrome and Apple’s Safari.

IT Toolbox
DECEMBER 15, 2023
Since May 2023, the malicious packages have been downloaded over 10,000 times. The post Windows and Linux Systems at Risk to PyPI Repository Malware Packages appeared first on Spiceworks.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Network World
OCTOBER 6, 2016
Spotify's ads crossed from nuisance over to outright nasty this week, after the music service’s advertising started serving up malware to users on Wednesday. The malware was able to automatically launch browser tabs on Windows and Mac PCs, according to complaints that surfaced online.

Network World
FEBRUARY 1, 2017
No single antimalware engine can keep up with all the malware out there. But how about 57 of 'em? [ 18 surprising tips for security pros. Discover how to secure your systems with InfoWorld's Security Report newsletter. ].

Dataconomy
FEBRUARY 14, 2025
The game was designed to contain malware that could steal users’ browser cookies and was available for at least a week before Valve removed it from its storefront and alerted users about potential risks to their PCs. According to SteamDB , the game was downloaded by an estimated 800 to 1,500 users before its delisting.

Network World
JUNE 7, 2016
Attackers are abusing the Windows Background Intelligent Transfer Service (BITS) to re-infect computers with malware after they've been already cleaned by antivirus products. The technique was observed in the wild last month by researchers from SecureWorks while responding to a malware incident for a customer.

Network World
FEBRUARY 6, 2017
After aggressively using JavaScript email attachments to distribute malware for the past year, attackers are now switching to less suspicious file types to trick users. Last week, researchers from the Microsoft Malware Protection Center warned about a new wave of spam emails that carried malicious.LNK files inside ZIP archives.

TechSpot
JUNE 23, 2021
A post by Palo Alto Networks' Brad Duncan (via ZDNet) explains that BazarLoader provides backdoor access to an infected Windows host. Once downloaded, criminals use the backdoor to send follow-up malware, such as ransomware, scan the environment, and exploit other vulnerable hosts on the network.

TechSpot
OCTOBER 19, 2020
As per Bleeping Computer, the malware is delivered through spam emails containing either malicious Word or Excel documents or download links. When opened, the attachments prompt users to ‘Enable Content’ to allow macros to run, which install the Emotet trojan.

The Verge
OCTOBER 6, 2021
If you think your PC is infected with some kind of malware or you just want to do a scan as part of a digital cleanup, Windows has a built-in security tool that can help you on your way — no third-party software to install or pay for. It’s called Windows Security. Windows Security’s built-in virus and threat protection feature.

SecureWorld News
APRIL 11, 2024
The Raspberry Robin malware, a heavily obfuscated Windows worm first identified in late 2021, has become one of the most prevalent threats facing enterprises today. According to HP's Threat Research Team , threat actors have recently been delivering Raspberry Robin through malicious Windows Script Files (WSF).

CTOvision
NOVEMBER 26, 2013
Solution provides real-time detection, identification, and mitigation of advanced malware that operates in endpoint volatile memory . product suite, combines Triumfant’s unique, patented malware detection software with new tools that can accurately track malware functionality operating in the volatile memory of the endpoint machine.

CTOvision
AUGUST 4, 2014
Extends Platform Coverage to Windows 8.1 releases as part of the Invincea platform focus specifically on the enterprise need for rapid adoption and ongoing management of large-scale Invincea deployments, including coverage for Microsoft’s recent Windows and Office product suites. . – bg. From Invincea. The FreeSpace 4.0

CTOvision
APRIL 7, 2014
in new contracts for advanced cybersecurity projects for defense and federal government agencies in the areas of cloud-based advanced malware analysis, spear-phishing attacks against Android, and big data analytics for compromise detection. In the first quarter of 2014, the company’s advanced research division—Invincea Labs—secured $8.1M

Dataconomy
JANUARY 10, 2025
malware, an infostealer targeting macOS, evades antivirus detection by employing an encryption mechanism drawn from Apple’s XProtect antivirus product. malware uses Apples encryption to evade detection Banshee 2.0 malware uses Apples encryption to evade detection Banshee 2.0 The Banshee 2.0

Network World
APRIL 12, 2017
The exploit allows a Word document to install malware onto your PC without you ever knowing it, giving the attackers full access to your machine. According to McAfee, the exploit works by connecting to a remote server controlled by the hackers, which will download a file that runs as a.hta file, a dynamic HTML file that is used in Word.

Galido
SEPTEMBER 2, 2018
Information Technology Blog - - The Best Free Antivirus Software for Windows 7-10 - Information Technology Blog. Over 8 years have gone after Windows 7 was introduced it’s as yet the most mainstream Windows out there. Bitdefender. Yet, there’s a catch: the amazing virus detection is all you’ll get.

SecureWorld News
AUGUST 8, 2022
Cybersecurity and Infrastructure Security Agency (CISA) and the Australian Cyber Security Centre (ACSC) released a joint Cybersecurity Advisory (CSA) providing details on the top malware strains of 2021. The top malware strains in 2021 included remote access Trojans (RATs), banking Trojans, information stealers, and ransomware.
Dataconomy
NOVEMBER 8, 2024
Cybersecurity experts have identified a new threat targeting Windows gamers: the malicious Winos4.0 has rapidly evolved into a sophisticated malware platform with extensive control capabilities over infected systems. The file extracts a dynamic link library (DLL) file that enables the malware to integrate into the system.

The Verge
JUNE 25, 2021
Microsoft announced yesterday that Windows 11 will require TPM (Trusted Platform Module) chips on existing and new devices. What is a TPM, and why do you need one for Windows 11 anyway? It can be used to encrypt disks using Windows features like BitLocker, or to prevent dictionary attacks against passwords.

SecureWorld News
MAY 1, 2023
Google has obtained a temporary court order to disrupt the distribution of CryptBot, a Windows-based information-stealing malware that has infected more than 670,000 computers in 2022. The harvested data is then sold to other attackers for use in data breach campaigns.
CIO Business Intelligence
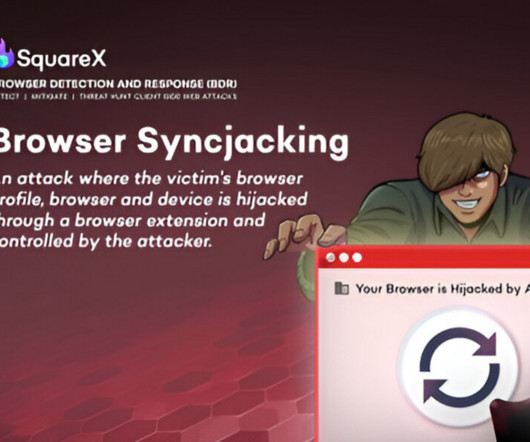
JANUARY 30, 2025
This is all done in an automated manner in a background window, making the whole process almost imperceptible to the victim. Thinking that they downloaded a Zoom updater, the victim executes the file, which ends up installing a registry entry that instructs the browser to become managed by the attackers Google Workspace.

CIO Business Intelligence
MAY 12, 2022
Locking the front door doesn’t help if the windows and back doors are open. Secure the windows. It detects applications that aren’t visible to administrators and allows you to create policies based on risk, such as prohibiting shares or downloads,” Vasudevan says. Take the native sharing functionality in Google Docs.

CIO Business Intelligence
NOVEMBER 23, 2022
Ransomware often starts from something as humble as someone in the organisation downloading the wrong file from an email. In addition, virtualised security software, such as Windows Defended Credential Guard and Application Guard are boosted through Intel’s own virtualization capabilities.

The Verge
JUNE 25, 2021
Windows 11 is arriving later this year as a free upgrade for Windows 10 users , but many are discovering that their hardware isn’t compatible. Windows 11 will only officially support 8th Gen and newer Intel Core processors, alongside Apollo Lake and newer Pentium and Celeron processors. Windows 11 support for AMD.

The Verge
JANUARY 21, 2022
Ransomware — malware that prevents you from accessing your files unless you pay the hacker that infected your computer — has been an issue plaguing computer users and businesses for years. Starting with Windows 10 , Microsoft has added features to its built-in Windows Security software that can help keep your computer safe from ransomware.
The Verge
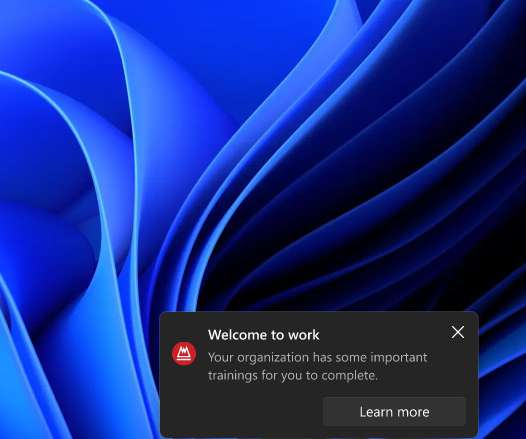
APRIL 5, 2022
If you’re an IT admin and you’ve always wanted to send messages to your Windows users, Microsoft is opening up a new option soon. IT admins will soon be able to send organizational messages to Windows 11 PCs, and they can appear on a lock screen, desktop, or above the taskbar. IT admins can generate Windows 11 messages.
Dataconomy
OCTOBER 22, 2024
When you delete files on a Windows PC, it will be put into the Recycle Bin folder. Virus or malware: It may be downloaded from website online or bundled with the software you are using that will maliciously delete your files. With it, you can recover deleted files in Windows 10 , 8, 7, and Windows Server.
Gizmodo
APRIL 9, 2021
Cybercriminals have been pushing Facebook users to download a Clubhouse app “for PC,” something that doesn’t exist. The app is actually a trojan designed to inject malware into your computer. The popular new invite-only chat app is only available on iPhone but worldwide interest in the platform has risen and users are… Read more.
CIO Business Intelligence
NOVEMBER 2, 2023
Organizations that follow the principle of least privilege can improve their security posture by significantly reducing their attack surface and risk of malware spread. In the early days of Windows operating systems up through Windows XP, almost any program a user would launch would have administrator-level privileges.
Dataconomy
MARCH 20, 2025
The ClearFake campaign has infected at least 9,300 websites, employing fake reCAPTCHA and Cloudflare Turnstile verifications to lure users into downloading malicious software, including Lumma Stealer and Vidar Stealer. These resources serve to fingerprint the victim’s system and download, decrypt, and display the ClickFix lure.

Dataconomy
MARCH 6, 2025
You were all set for a productive dayor maybe just ready to launch that game youve been obsessing overwhen Windows hit you with the cold, heartless message: “The program cant start because MSVCP140.dll Think of it as one of those essential cogs in the machine that is Windows. Let Windows work its magic. Keep reading.
Galido
NOVEMBER 21, 2019
This is so because, the presence of online malware, spyware, adware is something that cannot be ignored, hence, the need for more efficient, reliable and supportive antimalware like Malwarebytes was introduced. In other words, Malwarebytes works with the window defender to create a more protective mechanism for your system.

Galido
JANUARY 12, 2017
Each computer system may have a malware or viruses, including Linux. It is recommended that users install these antivirus softwares on the Linux operating system that can be downloaded via Internet. In order to better understand antivirus programs, it may be beneficial to firstly understand the malware itself. Linux Viruses.

SecureWorld News
NOVEMBER 12, 2020
First, however, let's look at the top 15 cyber threats organizations face right now, according to the report: Malware. Trends in Malware attacks. We can't look at all of these categories, but let's talk about the number one cyber attack threat of malware. 46,5%_of all malware in e-mail messages found in ‘.docx’

SecureWorld News
APRIL 21, 2022
The threat actors use social engineering to encourage individuals to download trojanized cryptocurrency applications on Windows or macOS operating systems. They use the apps to gain access to the victim's computer and install malware across the network environment, stealing private keys and exploiting other security gaps.
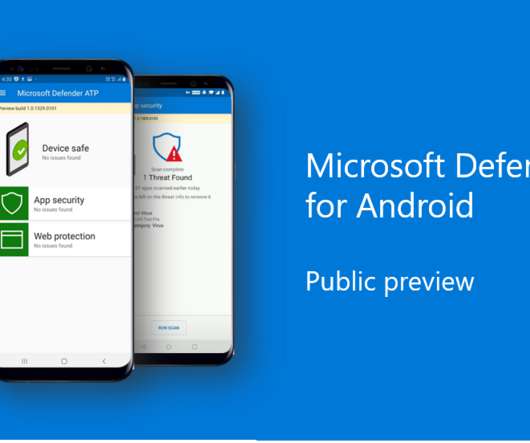
The Verge
JUNE 23, 2020
The software giant revealed that Windows Defender was making its way to both iOS and Android earlier this year , but didn’t fully detail what to expect. The public preview for Android will include protection against phishing and go a step further than Google’s built-in malware protection to offer signature-based malware detection.

Galido
JULY 2, 2016
Cryptowall, the now-infamous encryption malware that locks files for ransom, has been updated. Known as Cryptowall 4, the ransomware infects Windows machines, encrypts files, and demands users cough up crypto-cash to unlock their documents. Crytowall encrypts your files and holds them ransom until you pay for a decryption key.

SecureWorld News
MARCH 10, 2025
From simple breaches to complex automation Traditionally, insider threats involved straightforward breaches: an employee downloads sensitive files ( Stuxnet, anyone? ), leaks confidential information, or manipulates company data for personal gain. Create custom malware that adapts to countermeasures in real time.

SecureWorld News
JUNE 13, 2023
The new Beep malware is top of mind for organizations and individuals. We are continuing to observe an unyielding surge in the volume of cyberthreats, including advanced malware, botnets, ransomware, cryptojacking, and more," said Callie Guenther, Senior Manager of Cyber Threat Research at Critical Start, in a press release.

Dataconomy
FEBRUARY 12, 2024
Malware continues to plague organizations and individuals alike and one of the more insidious strains in recent times is the Raspberry Robin malware. Malware – malicious software crafted with harmful intent – acts as their weapon of choice.

SecureWorld News
SEPTEMBER 25, 2021
Whether it is ransomware, other types of malware, or any number of cyberattacks, threat actors keep inventing new techniques to cause disruption. In a blog post, Neel Mehta, Information Security lead for Google, explains how a hacker has managed to break certificate code parsing to invade email inboxes and infect users with malware.

SecureWorld News
SEPTEMBER 25, 2024
A growing threat: malvertising's new tactics Malvertising, or malicious advertising, involves cybercriminals embedding malware or phishing traps in online ads. Similarly, ads mimicking well-known corporate tools like Slack have been reported, where initial clicks appear harmless, but later steps encourage users to download malicious software.

SecureWorld News
APRIL 4, 2023
The attackers compromised the Windows and Mac versions of the application, leading to many 3CX customers downloading a trojanized version of the app. The company has advised customers to uninstall the Electron app for Mac and Windows and use the web app (PWA) version until a clean app is developed.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content