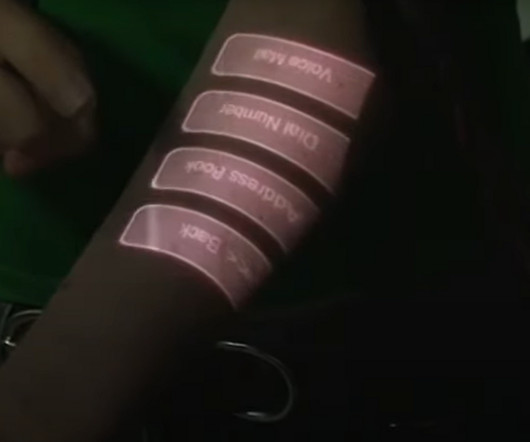
The Wireless Attack Toolkit
CTOvision
AUGUST 15, 2013
By BryanHalfpap Wireless security is all about implementation. How much and what you leak depends on your wireless driver, operating system, and the networks that you’ve connected to in the past. Potentially any of your past network connections that weren’t encrypted are targets if they are beaconed for by your hardware.














































Let's personalize your content