Remote working: This new Microsoft VPN aims to make your mobile devices more secure
Tech Republic Security
NOVEMBER 19, 2020
Microsoft has delivered a managed VPN for mobile devices -- using a Linux container.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Tech Republic Security
MAY 5, 2022
The post Google, Apple, Microsoft promise end to passwords, courtesy of your mobile phone appeared first on TechRepublic. Adopting a new authentication method from the FIDO Alliance, the three major OS vendors will let you use encrypted credentials stored on your phone to automatically sign you into your online accounts.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CIO Business Intelligence
DECEMBER 24, 2024
The incident prompted some CIOs to rethink their dependence on cloud infrastructure, and it caused Microsoft to focus more on kernel-level access for other software packages. Meanwhile, Delta Airlines filed a $500 million lawsuit against CrowdStrike and Microsoft and reconsidered its use of Microsoft products.

Forrester IT
OCTOBER 27, 2023
Microsoft completed its largest ever acquisition of Activision Blizzard earlier this month. Buried under the lede is the fact that it now owns King, a hugely successful mobile advertising platform with over $300 million in advertising revenue annually.

Tech Republic Security
JANUARY 30, 2023
The post Unphishable mobile MFA through hardware keys appeared first on TechRepublic. With Azure AD and FIDO security keys, you can make MFA more secure and avoid having to provision certificates on everyone’s phones.

CIO Business Intelligence
DECEMBER 10, 2024
Its a common skill for developers, software engineers, full-stack developers, DevOps engineers, cloud engineers, mobile app developers, backend developers, and big data engineers. Its used for web development, multithreading and concurrency, QA testing, developing cloud and microservices, and database integration.

Network World
OCTOBER 25, 2024
llwyn Sequeira, founder and CEO of Highway 9 Networks, shared how this company used AI and machine learning techniques to significantly reduce the implementation and configuration time for their private mobile cloud solution on a campus. “We AI will also help to accelerate the deployment and provisioning of WAN capabilities.

CIO Business Intelligence
NOVEMBER 15, 2023
This year’s Microsoft Ignite developer conference might as well be called AIgnite, with over half of the almost 600 sessions featuring artificial intelligence in some shape or form. Here’s some of the top AI news CIOs will want to take away from Microsoft Ignite 2023. The new Copilot will be generally available from Dec.

Anoop
APRIL 25, 2024
Subscribe to YouTube Channel [link] and Facebook Page to get the latest updates [link] The post Microsoft Introduced CrowdStrike Falcon as a Mobile Threat Defense Partner with Intune appeared first on HTMD Community Blog #1 Modern Device Management Guides by Krishna R. Hello - Here is the new HTMD Blog Article for you.

CIO Business Intelligence
SEPTEMBER 20, 2024
Microsoft Copilot — integrated with the power of Windows 11 Pro — provides a strategic platform for streamlining operations, improving customer experiences, and empowering store associates. Microsoft Copilot integrates seamlessly into retail environments, offering AI-powered personalization. Click here to book a discovery call.

GeekWire
DECEMBER 23, 2024
Tong was at Microsoft for more than 11 years, including a stint as vice president of marketing for Microsoft Office. He’s seen how the internet, the cloud, and then mobile shook up the tech world. “We’re very lucky to have this Microsoft heritage,” Tong said.

GeekWire
MAY 9, 2024
(GeekWire File Photo / Nat Levy) In a surprise reveal, Microsoft said Thursday it plans to launch a mobile gaming store later this year. In November, Xbox head Phil Spencer that the company was “talking to other partners” to potentially launch a mobile store. A recent report from Newzoo lists mobile gaming as making up $90.5

GeekWire
MARCH 25, 2025
LinkedIn Photo) Microsoft’s Teresa Hutson has taken the role of corporate vice president for the company’s newly created Trusted Technology Group. Microsoft is modifying its mission-focused “four pillars,” which include working to expand opportunities, earn trust, protect fundamental rights and advance sustainability.

CIO Business Intelligence
OCTOBER 19, 2023
Visualize all the services you use Power BI has hundreds of content packs, templates, and integrations for hundreds of data services, apps, and services — and not just Microsoft ones such as Dynamics 365 and SQL Server. According to Microsoft, an organizations’ use of Power BI data nearly doubles when the app is pinned in Teams.

Network World
MARCH 19, 2025
An industry generative artificial intelligence (genAI) alliance, the AI Infrastructure Partnership (AIP), on Wednesday announced that xAI, Nvidia, GE Vernova, and NextEra Energy were joining BlackRock, Microsoft, and Global Infrastructure Partners as members.

CIO Business Intelligence
JULY 19, 2023
Since Satya Nadella took the helm in 2014, Microsoft has doubled down on its support for non-Microsoft technologies. Its commitment to Linux turned what might have been a Windows Server-based cloud computing backwater into the Microsoft Azure powerhouse, the only public cloud to give the AWS juggernaut a serious run for its money.

CIO Business Intelligence
OCTOBER 12, 2022
Microsoft has heard them loud and clear, and at its Ignite 2022 show in Seattle this week, it introduced a range of new governance capabilities and other enhancements for its Power automation platform. Power to the people. First previewed in July, it’s now generally available. Checks and balances. Environmental awareness.

CIO Business Intelligence
APRIL 20, 2023
Cloud adoption was the need, and AI on cloud is imperative today,” says Nilendu Pattanaik, Global Head Business Applications Practice, Microsoft Business Unit, at Tata Consultancy Services (TCS). With AI and Microsoft Cloud, the right product at the right time can be supplied, stocked, sold, and served with a superior impact. “An

CIO Business Intelligence
JUNE 29, 2022
For many enterprises, Microsoft Azure has become a central hub for analytics. Taking the broadest possible interpretation of data analytics , Azure offers more than a dozen services — and that’s before you include Power BI, with its AI-powered analysis and new datamart option , or governance-oriented approaches such as Microsoft Purview.

CIO Business Intelligence
APRIL 17, 2023
Every new portal and mobile app expand the attack surface and give hackers new opportunities to exploit vulnerabilities. Challenges for fraud risk management Fraud is a big and a worthwhile business for today’s online criminals, who troll the internet and insert data-stealing malware into vulnerable sites and mobile apps.

CIO Business Intelligence
OCTOBER 23, 2024
September and October saw more layoffs from companies such as Microsoft, Meta, Apple, Dell, Samsung, and Qualcomm. Although not all technical roles, these layoffs have contributed to unemployment levels in IT not seen for some time, increasing the available pool of IT candidates.

Network World
DECEMBER 2, 2024
Ellis said he liked the storage browser, finding it “really interesting, and [it] has a lot of possibilities for web applications, mobile apps, and shared app storage for distributed teams. Focus on customer experience Kimball saw the fact that Google and Microsoft were not referenced in the announcements as part of the strategy. “I
CIO Business Intelligence
FEBRUARY 6, 2025
Within two years, it will be virtually impossible to buy a PC, tablet, laptop, or mobile phone without AI, John-David Lovelock, distinguished vice president analyst at Gartner, recently told CIO.com. OEMs that have shipped or are readying AI PCs for 2025 or 2026 include Dell, Acer, Asus, HP, Lenovo, Samsung, and Microsoft.

Dataconomy
FEBRUARY 27, 2025
Microsoft Corp. billion parameters, enabling it to run efficiently on mobile devices. billion parameters, enabling it to run efficiently on mobile devices. Featured image credit: Microsoft Phi-4-mini and Phi-4-multimodal features Phi-4-mini is a text-only model that incorporates 3.8 Googles Gemini Flash 2.0

CIO Business Intelligence
OCTOBER 24, 2024
In some cases, the AI add-ons will be subscription models, like Microsoft Copilot, and sometimes, they will be free, like Salesforce Einstein, he says. Free the AI At the same time, most organizations will spend a small percentage of their IT budgets on gen AI software deployments, Lovelock says. growth in device spending.

GeekWire
APRIL 1, 2025
Patti Thibodeau, Microsoft Archivist, left, shows Microsoft’s Albuquerque team photo and a related memo. GeekWire Photo / Todd Bishop) [Editors Note: Microsoft @ 50 is a year-long GeekWire project exploring the tech giants past, present, and future, recognizing its 50th anniversary in 2025.] REDMOND, Wash.

SecureWorld News
FEBRUARY 20, 2025
Microsoft's recent announcement of the Majorana 1 chip marks a significant leap toward scalable quantum computing, potentially accelerating the timeline for a commercially viable quantum computer. With this breakthrough, Microsoft claims quantum computers capable of solving industrial-scale problems could be realized in years, not decades.

TechSpot
OCTOBER 24, 2024
Microsoft recently introduced a change in how to use Word, Excel, and PowerPoint file types on Android and iOS devices. The new behavior is reserved for "hub" mobile experiences, chiefly OneDrive, Outlook, and Teams. Read Entire Article
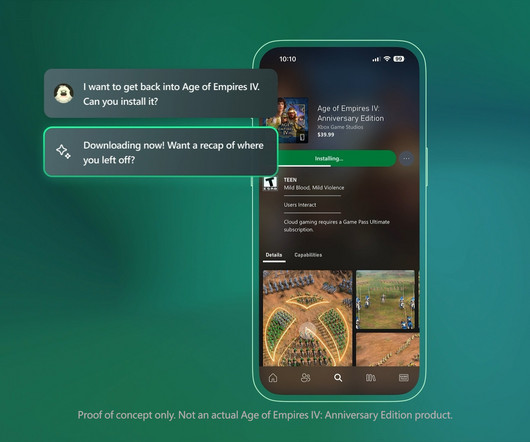
GeekWire
MARCH 13, 2025
This official Microsoft mock-up demonstrates how Copilot can be used for processes like picking up an old run through a game. Microsoft Image) In advance of this years Game Developers Conference, Microsoft revealed a new version of its AI-powered personal assistant Copilot thats designed for the Xbox platform.

CIO Business Intelligence
DECEMBER 18, 2024
Or the classic Microsoft support scam in which threat actors claiming to be from Microsoft support call customers and offer to fix nonexistent issues with their device, often gaining access to the customers computer and personal data in the process. This sort of attack is a novel evolution of a traditional vishing attack.
Anoop
MAY 14, 2024
Subscribe to YouTube Channel [link] and Facebook Page to get the latest updates [link] The post Universal Print Integration with Microsoft 365 Mobile App for Android Printing appeared first on HTMD Community Blog #1 Modern Device Management Guides by Krishna R. Hello - Here is the new HTMD Blog Article for you. Enjoy reading it.

GeekWire
DECEMBER 18, 2024
Microsoft CEO Satya Nadella unveils Copilot + PCs, a linchpin of the companys plan to reinvent Windows, during a special event in Redmond in May 2024. GeekWire Photo / Todd Bishop) Editors Note: Microsoft @ 50 is a year-long GeekWire project exploring the tech giants past, present, and future, recognizing its 50th anniversary in 2025.

GeekWire
DECEMBER 17, 2024
Microsoft recently rolled out a new Home experience for its Xbox app on Windows PC. The report consciously focuses on the PC and console markets, while mostly omitting the much larger mobile sector. This is similar to the issues that mobile and PC studios have reported with the free-to-play publishing model.

Network World
OCTOBER 2, 2024
“This accelerates our research and development efforts and strengthens the European quantum ecosystem, paving the way for advances in mobility, healthcare and sustainable technologies.” This story originally appeared on Computerwoche.

GeekWire
NOVEMBER 24, 2024
… Read More Amazon hires former Microsoft and SAP exec Julia White as new AWS marketing chief Julia White, a longtime Microsoft executive who spent the past four years at SAP, has been named the chief marketing officer and vice president at Amazon Web Services. … Read More GeekWire 200 update: A new No.

Network World
AUGUST 29, 2024
NGINX Plus is F5’s application security suite that includes a software load balancer, content cache, web server, API gateway, and microservices proxy designed to protect distributed web and mobile applications.

CIO Business Intelligence
MARCH 12, 2025
But even the IT environments of companies in less complex industries often now resemble a conglomeration of local data centers, virtual machines, mobile devices and cloud services. They combine public cloud services from AWS, Microsoft Azure or Google Cloud, for example. AWS vs. Azure: Which platform is best for which application?

CIO Business Intelligence
APRIL 25, 2023
consumers use mobile banking channels, and 70% said mobile banking is now their primary way of accessing their accounts. “Most people do not want to go into a bank to do banking. For example, Microsoft Dynamics 365 Copilot, the world’s first copilot in both CRM and ERP, brings next-generation AI to every line of business. “As

TechSpot
OCTOBER 25, 2023
Nadella said that in retrospect, he believes Microsoft could have made things work by perhaps reinventing the relationship between PCs, tablets, and phones. Read Entire Article

TechSpot
MAY 16, 2024
This isn't Microsoft's first rodeo with accessible controllers. Its Xbox Adaptive Controller from 2018 was a game-changer, allowing those with limited mobility to craft a control setup tailored to their needs. But the Proteus takes it to a whole new level of flexibility and customization. Read Entire Article
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?




Let's personalize your content