Make Application Security A Top Priority
Forrester IT
MARCH 23, 2021
When we launched the most recent Forrester Analytics Business Technographics® Security Survey, it was summer of 2020. That meant a lot of application development, as […].
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Forrester IT
MARCH 23, 2021
When we launched the most recent Forrester Analytics Business Technographics® Security Survey, it was summer of 2020. That meant a lot of application development, as […].

CTOvision
FEBRUARY 24, 2014
By Bob Gourley The Open Web Application Security Project (OWASP) has just releases the results of a Survey of global CISO s. OWASP is an international organization and an open community dedicated to helping organizations conceive, develop, acquire, operate and maintain applications that can be trusted.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Generative AI Deep Dive: Advancing from Proof of Concept to Production
Reimagining Cybersecurity Training: Driving Real Impact on Security Culture
Don’t Get Left Behind: Leveraging Modern Product Management Across the Organization

CIO Business Intelligence
APRIL 25, 2024
However, barriers such as adoption speed and security concerns hinder rapid AI integration, according to a new survey. Of the 750 CIOs around the world surveyed by Lenovo, 81% said they are already leveraging third-party AI Tools or deploying a mix of third-party and proprietary AI.

Network World
MAY 22, 2024
Today’s enterprises need more help managing and securing their distributed networking environments than they ever have, Cisco concludes in its Global Networking Trends Report. 2024 Cisco Global Networking Trends Report As networks scale to handle new applications in the data center and cloud, the threat landscape grows, Davidson stated.

Advertisement
Think your customers will pay more for data visualizations in your application? Discover which features will differentiate your application and maximize the ROI of your embedded analytics. Five years ago they may have. But today, dashboards and visualizations have become table stakes. Brought to you by Logi Analytics.

Forrester IT
MAY 9, 2022
Attackers have stepped up their application game in the past year. Sixty-two percent of organizations surveyed by software supply chain security vendor Anchore have been impacted by a software supply chain attack in the past year.

CIO Business Intelligence
NOVEMBER 13, 2023
Overall, open source has incredible potential to help transform the way mainframe applications are managed, but it comes with risks that need to be properly addressed. So, where do businesses and IT leaders stand on the use of open source in the context of mainframe security? What are their concerns?

Tech Republic Security
NOVEMBER 18, 2021
Only 25% of consumers surveyed by NTT Application Security said they'd take their online business elsewhere following a data breach.
CIO Business Intelligence
AUGUST 2, 2023
Generative AI is already making deep inroads into the enterprise, but not always under IT department control, according to a recent survey of business and IT leaders by Foundry, publisher of CIO.com. The survey found tension between business leaders seeking competitive advantage, and IT leaders wanting to limit risks.

SecureWorld News
DECEMBER 8, 2022
As the pace of software development increases, security teams are struggling to keep up. And, the widespread use of continuous integration and continuous delivery (CI/CD) to bridge gaps between developers and operations by enforcing automation can further exacerbate the gulf between development and security.

Network World
OCTOBER 11, 2023
In the rush to deploy generative AI , many organizations are sacrificing security in favor of innovation, IBM warns. Among 200 executives surveyed by IBM, 94% said it’s important to secure generative AI applications and services before deployment. To read this article in full, please click here

CIO Business Intelligence
NOVEMBER 14, 2023
In the last decade, the technology industry experienced a massive shift toward the cloud where every company no matter the industry developed and deployed cloud-native applications. According to a recent survey, more than 75% of organizations are deploying new or updated code to production weekly, and almost 40% are committing new code daily.

CIO Business Intelligence
MARCH 6, 2024
Organisations are wrestling to disentangle work from a physical location as they adjust to flexible work models, and one of the biggest challenges has been dealing with endpoint security. Securing endpoint devices is often considered secondary to identity management, data security, and software hacking. Remote Work, Security

Network World
SEPTEMBER 6, 2023
In 2019, Gartner created the term secure access service edge (SASE) to describe a cloud-based service that combines networking and security in order to give remote workers safe access to internet-based resources. To read this article in full, please click here

CIO Business Intelligence
NOVEMBER 13, 2023
Mainframe developers face unique challenges when ensuring their IT environments are secure. Tools like open source have helped give a boost to software development, but it also means security needs to always be top of mind. Chief among those challenges? What’s the state of DevSecOps today?

CIO Business Intelligence
JULY 6, 2023
Threats are emerging at a speed that makes it difficult for internal security practitioners to keep pace. There are zero-day attacks that exploit vulnerabilities before security teams are even aware of them. DDoS attacks that target networks, applications, and APIs can seemingly come out of nowhere. And SECaaS gives you that.”
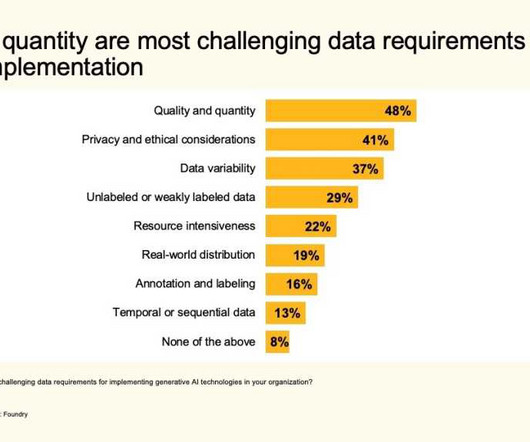
CIO Business Intelligence
OCTOBER 11, 2023
For its AI Priorities Study 2023 , Foundry surveyed IT decision-makers who have either implemented AI and generative AI technologies in their organizations, have plans to, or are actively researching them. Top of those AI priorities for now is generative AI, with 56% of respondents eager to learn more about it.

TM Forum
NOVEMBER 15, 2022
Orange, Telefónica, and Verizon each made moves this week to expand their security service offerings for enterprises, signaling the growing importance of managed security among revenue growth opportunities for communications service providers (CSPs). Orange acquires Swiss security specialist. for an undisclosed sum.

CIO Business Intelligence
MARCH 3, 2024
For its 2023 Security Priorities report, Foundry surveyed 790 IT security workers to understand their projects and priorities. Printers are often not subject to the rigorous security measures routinely applied to computing devices; for example, complex passwords and rigorous patching and software update regimes.
TM Forum
APRIL 29, 2022
with security set to be one of the key areas of investment. The index reports that 93 % of the 2,000 small and medium companies surveyed for the report intend to maintain digital investment, with 45% of these planning an average increase in spending of 24%. Gartner estimates that. worldwide IT spending will total $4.4 up 4% from 2021.

Tech Republic Security
JUNE 30, 2020
86% of developers polled in a recent survey said every single aspect of appsec hinders their ability to push code.

CIO Business Intelligence
NOVEMBER 13, 2023
According to a recent survey by Rocket Software, 51% of IT leaders indicated that they run either all or the majority of their core business applications on the mainframe. This means the security of the mainframe is absolutely essential. Read on to learn their perspective on mainframe security.

CIO Business Intelligence
DECEMBER 19, 2023
In practice, if an enterprise spends the majority of its IT budget on SaaS applications, cloud storage, application development, etc., To protect these cloud investments, the lion’s share of cybersecurity budgets today must go towards cloud security. Today, the majority of enterprise investment revolves around the cloud.

CIO Business Intelligence
MAY 9, 2023
According to the Rocket Software Survey Report 2022: The State of the Mainframe , four out of five IT professionals see the mainframe as critical to business success. With that in mind, what can businesses do to modernize their applications effectively? Without, it can create security and compliance risks—and be difficult to maintain.

CIO Business Intelligence
MARCH 18, 2024
There’s a reason that—according to a Rocket Software survey , over half (51%) of IT leaders rely on mainframe systems to handle all, or nearly all, core business applications. But even for a highly secure system like the mainframe, risks still exist. IT leaders face an increasingly complex security landscape.
CIO Business Intelligence
NOVEMBER 3, 2022
By Milan Shetti, CEO Rocket Software According to a recent Rocket Software survey , 80% of IT professionals categorize the mainframe as critical to their business. One technology that modern mainframes need is secure open-source software. Read on to learn more about why modern mainframes need secure open source.

CIO Business Intelligence
MARCH 17, 2023
CIOs have shifted toward building their own web application platforms with a set of best-in-class tools for more flexibility, customizations, and agile DevOps. Platform development includes design, coding, testing, securing, and deploying. Enterprise Applications, SaaS This choice, however, isn’t right in all circumstances.

CIO Business Intelligence
FEBRUARY 7, 2023
For as long as organizations have been interested in moving resources to the cloud, they’ve been concerned about security. More than two-thirds of the 850 IT leaders who participated in a recent Foundry survey said they were accelerating their cloud migration. It’s called a disaster. BrendenBosch Except it is not fine print.

SecureWorld News
MAY 21, 2024
So, we are more and more dependent on the security and resilience of the systems running critical infrastructure—maritime in this case. A Sector Specific Agency (SSA) was identified for each critical sector, with the Department of Homeland Security (Transportation Security Administration and U.S.

CIO Business Intelligence
MAY 31, 2023
Most applications built today leverage Application Programming Interfaces (APIs), code that makes it possible for digital devices, applications, and servers to communicate and share data. API mismanagement: Security risk can occur if the API is not properly managed and audited, including versioning and documentation of code.

CIO Business Intelligence
APRIL 29, 2024
As organizations roll out AI applications and AI-enabled smartphones and devices, IT leaders may need to sell the benefits to employees or risk those investments falling short of business expectations. Nearly three-quarters of employees surveyed said they believe AI devices will make them more productive.

CIO Business Intelligence
JUNE 13, 2023
Nearly 15% of all organizations surveyed are using 7 to 10 information management systems. These systems are not integrated in nearly 75% of organizations, which poses challenges to compliance adherence and reporting related to electronic discovery (eDiscovery), privacy, information security, and overall governance and compliance.

Galido
AUGUST 7, 2016
And how do you feel about the security of the apps you install? Arxan recently did a 5th annual State of Application Security report, which takes an in-depth look into the security of some of the most popular mobile health and mobile finance applications available. How safe is your app?

GeekWire
MARCH 14, 2024
.” Numerous states have banned the TikTok app on government-owned devices due to security concerns. The House bill, called the Protecting Americans from Foreign Adversary Controlled Applications Act , states that its aim is to “protect the national security of the United States.” ”

Forrester IT
SEPTEMBER 6, 2022
New applications and features were built, deployed, and released at a rate that previously would not have seemed possible. In Forrester’s Developer Survey, 2022, 67% of developers said they release incremental software changes into production at least monthly, and […].

Tech Republic Security
MAY 16, 2017
Despite understanding the risks, a majority of CEOs and business decision makers do not adhere to enterprise security practices, according to a new survey from Code42.
CIO Business Intelligence
AUGUST 18, 2022
For IT and network security teams, the challenge is to secure their environments, regardless of where people are working. The WAN architecture must cater to the needs of office and remote workers with parity in terms of routing policies, security profile, and management of the WAN.” . Shifting locations and network connections.

Forrester IT
FEBRUARY 22, 2023
Zero Trust has seen an increase in adoption over the past few years — Forrester’s Security Survey, 2022, shows that 83% of global large enterprises are reporting that senior leadership has committed their organizations to the adoption of Zero Trust. Aspects of the Zero Trust model continue to be misunderstood, however.

CIO Business Intelligence
SEPTEMBER 14, 2022
Does your organization need to improve security and upgrade its IT infrastructure? These priorities are in response to an ever-evolving business and security landscape. How to balance security with resiliency. These implementations have also led to security gaps and vulnerabilities. If so, you’re not alone.

CIO Business Intelligence
MAY 20, 2024
Artificial intelligence and machine learning Unsurprisingly, AI and machine learning top the list of initiatives CIOs expect their involvement to increase in the coming year, with 80% of respondents to the State of the CIO survey saying so. Other surveys offer similar findings. 1 priority among its respondents as well. For Rev.io

Cloud Musings
MARCH 10, 2014
Today PerspecSys announced the results of a survey conducted at the 2014 RSA Conference concerning the attitudes and policies of organizations towards cloud-based security. In fact, 66 percent of security pros still view the cloud as more difficult to secure than on-premise options.”

CIO Business Intelligence
JULY 11, 2022
All these variables force the need for organizations to transform their security postures to protect against cloud infrastructure vulnerabilities. However, the increased complexity of a distributed application architecture brought on by digital transformation continues to challenge even the largest security operations.

CIO Business Intelligence
MARCH 21, 2024
DSAG, a group representing SAP users in Germany, Austria and Switzerland, also released data from a survey of its members. The DSAG members surveyed are critical of SAP’s S/4HANA cloud strategy,” he said in a statement. Only 13% of those surveyed had a positive opinion, just under half had a negative one.”

Kitaboo
DECEMBER 29, 2023
It is imperative that Educational Technology , popularly termed as EdTech introduces stringent and robust security measures so that the safety of data and development is not compromised. The security of educational technology depends on the platform or application it uses.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content