CIOs Want To Run Their IT Department Like Adobe
The Accidental Successful CIO
APRIL 10, 2019
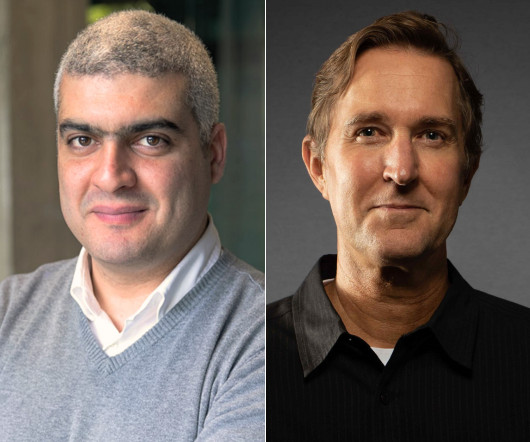
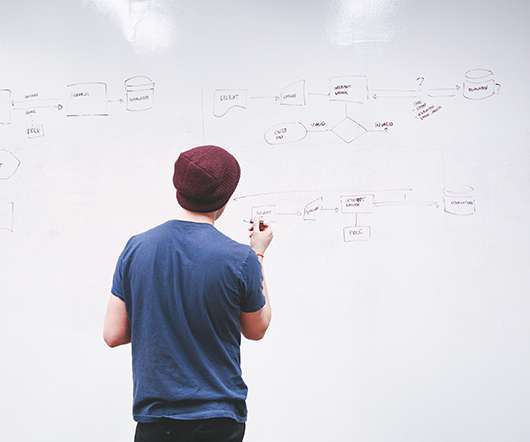
Adobe has a satisfied workforce, how can CIOs have the same thing? Image Credit: a_bul16. Being the person with the CIO job is hard work. You try and you try and you try to do a good job but it always seems like you are somehow falling further and further behind. There is so much work to do in regards to the importance of information technology that you only dream of being able to do all of the things that you should be doing in order to make your IT department as good as it could be.



































Let's personalize your content