AI Workloads Require Infrastructure Upgrades
Information Week
MARCH 15, 2022
Artificial intelligence workloads often require special infrastructure that previously was not considered needed for other demanding computational jobs.

Information Week
MARCH 15, 2022
Artificial intelligence workloads often require special infrastructure that previously was not considered needed for other demanding computational jobs.
Association of Information Technology Professional
MARCH 14, 2022
A reporting analyst is the link between raw enterprise data and the management team. Could this be your next move?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Forrester IT
MARCH 17, 2022
The average computer monitor, with 1080p resolution, has a grand total of 2,073,600 pixels. Sure, you can still see the image if you’re missing a few thousand pixels, but the clarity isn’t as sharp. Each pixel matters. Similarly, each data point matters in order to give you the complete picture of a market or a […].

Mick's IT Blog
MARCH 16, 2022
Recently, we needed a report of the last boot time of all servers. I wrote this PowerShell script that queries AD for a list of all windows servers and then does a WMI query on each server for the LastBootUpTime. It then calculates the number of days and writes this to an object with the computer name and the number of days since the last reboot. It will write this info to a CSV file.
Speaker: Maher Hanafi, VP of Engineering at Betterworks & Tony Karrer, CTO at Aggregage
Executive leaders and board members are pushing their teams to adopt Generative AI to gain a competitive edge, save money, and otherwise take advantage of the promise of this new era of artificial intelligence. There's no question that it is challenging to figure out where to focus and how to advance when it’s a new field that is evolving everyday. 💡 This new webinar featuring Maher Hanafi, CTO of Betterworks, will explore a practical framework to transform Generative AI prototypes into

Tech Republic Security
MARCH 18, 2022
If you are interested in pursuing a career in cybersecurity and don't know where to start, here's your go-to guide about salaries, job markets, skills and common interview questions in the field, as well as the top security software. The post How to become a cybersecurity pro: A cheat sheet appeared first on TechRepublic.
Anoop
MARCH 17, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Windows Package Manager & SCCM integration options, If there is any? How to Install the app using WinGet Tool and Configuration Manager (aka MEMCM). The post Install Uninstall Apps from Windows Package Manager using WinGet Tool and SCCM appeared first on HTMD Blog #1 by Anoop C Nair.
Information Technology Zone brings together the best content for IT professionals from the widest variety of industry thought leaders.

Spearline Testing
MARCH 17, 2022
Call centers are the core of today’s industry. Every successful company has a call center to engage with its customers, addressing their needs and providing assistance. It is vital to ensure that these customer engagements build a strong customer relationship. Leading businesses are always on the lookout for opportunities to improve the customer experience.

Tech Republic Security
MARCH 15, 2022
NCC Group’s study outlines the use cases for BCIs as well as the security risks associated with using them. The post Brain Computer Interfaces may be the future, but will they be secure? appeared first on TechRepublic.
Anoop
MARCH 16, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post How to Upgrade SCCM SQL Server to 2019 | Primary Site Database appeared first on HTMD Blog #1 by Anoop C Nair.

Information Week
MARCH 18, 2022
There are five core steps that allow companies to bring control, structure, and strategy to their intelligent automation projects, ensuring that the full value of these projects can be realized.

Speaker: Speakers:
They say a defense can be measured by its weakest link. In your cybersecurity posture, what––or who––is the weakest link? And how can you make them stronger? This webinar will equip you with the resources to search for quality training, implement it, and improve the cyber-behaviors of your workforce. By the end of the hour, you will feel empowered to improve the aspects of your security posture you control the least – the situational awareness and decision-making of your workforce.

Tech Republic Big Data
MARCH 18, 2022
If you are interested in pursuing a career in data science, this primer will help you learn about the hottest job markets, necessary skills, salaries, training resources and more. The post How to become a data scientist: A cheat sheet appeared first on TechRepublic.

Tech Republic Security
MARCH 15, 2022
Don’t let mobile malware ruin your day or your device. Be aware of how this threat happens and take good precautions to avoid it. The post Mobile malware is on the rise: Know how to protect yourself from a virus or stolen data appeared first on TechRepublic.

Anoop
MARCH 14, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post Upgrade Windows 10 21H2 using SCCM Task Sequence | Best Guide appeared first on HTMD Blog #1 by Jitesh Kumar.

Information Week
MARCH 17, 2022
As the invasion of Ukraine continues, Russian citizens have turned to virtual private networks — boosting demand for the software by 27x — to circumvent the government's blocks on social media and news sites critical of the war.

Advertisement
Generative AI is upending the way product developers & end-users alike are interacting with data. Despite the potential of AI, many are left with questions about the future of product development: How will AI impact my business and contribute to its success? What can product managers and developers expect in the future with the widespread adoption of AI?

CIO Business Intelligence
MARCH 18, 2022
Accenture hires thousands of people each year. It’s an expensive process that traditionally has involved flying people to central hubs for training and orientation. Two years ago, the consulting giant started shipping many of its recruits virtual reality headsets instead. At the same time, it created a virtual world or “metaverse” that enables employees to socialize, form teams, conduct training, and collaborate.

Tech Republic Security
MARCH 17, 2022
CISA adds 15 known exploited vulnerabilities to its catalog and BlackBerry researchers warn of a new ransomware-as-a-service family. The post Cybersecurity news: LokiLocker ransomware, Instagram phishing attack and new warnings from CISA appeared first on TechRepublic.
Anoop
MARCH 14, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post Use Microsoft Teams to Record Screen on Windows 11 PC appeared first on HTMD Blog #1 by Anoop C Nair.

Information Week
MARCH 17, 2022
The shift to zero trust will require IT leaders to re-think how they apply security controls as they seek to eliminate the pervasive trust extending through their systems of access.

Advertiser: GEP
Procurement and supply chain leaders are presented with their fair share of challenges, with a host of tools and strategies to resolve them. That said, what’s the best path forward to leverage this year’s trends? In this recap of a recent GEP-WBR webinar, 7 Leadership Themes for Procurement & Supply Chain Leaders in 2024, GEP’s Pramod Sethumadhavan explores seven vital leadership trends that will help guide procurement and supply chain decision-makers.

The Verge
MARCH 17, 2022
An instructor at the Fort Leonard Wood Chemical School, who is designated as an agent handler, carries the VX nerve agent to contaminate a jeep in one of the eight chambers used for training chemical defense on April 18, 2003 at Fort Leonard Wood, Missouri. | Photo by Brendan Smialowski/Getty Images. It took less than six hours for drug-developing AI to invent 40,000 potentially lethal molecules.

Tech Republic Security
MARCH 14, 2022
One lesser-known aspect of non-fungible tokens is their vulnerability to cybercrime. Learn how you can protect yourself and your company from the potential risks of NFTs. The post NFTs: The growing cybercrime risks and how to avoid them appeared first on TechRepublic.
Anoop
MARCH 18, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post Modern Day Ransomware Threats You Must Know About and How to Prevent Them appeared first on HTMD Community Blog #1 Modern Device Management Guides - Windows 11 | SCCM | ConfigMgr | Intune | AVD | Windows 10 | Windows 365 | Cloud PC by Admin.

Information Week
MARCH 15, 2022
As organizations face ongoing staffing shortages, CIOs require supplemental resources to stay afloat. Among these lifeboats are IT service providers.
Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

CIO Business Intelligence
MARCH 17, 2022
Data analytics is a domain in constant motion. Early in 2020, it seemed clear that organizations would continue to invest heavily in analytics to support their digital transformations. The COVID-19 pandemic emerged as a major disruptor. Early in the pandemic, it seemed organizations might waylay data and analytics advancements to retrench and focused on other pressing priorities like enabling a remote workforce.

Tech Republic Security
MARCH 17, 2022
The first line of defense against ransomware lies with email authentication. Learn more information about how to take a proactive approach to cyber attacks. The post Email authentication helps governments and private companies battle ransomware appeared first on TechRepublic.

GeekWire
MARCH 12, 2022
Amazon’s Seattle headquarters. (GeekWire Photo). Amazon is telling employees they can work at an alternative location due to recent crime around its downtown Seattle office at 300 Pine St. “Given recent incidents near 3rd and Pine, we’re providing employees currently at that location with alternative office space elsewhere. We are hopeful that conditions will improve and that we will be able to bring employees back to this location when it is safe to do so,” a spokesperson said in a

Information Week
MARCH 15, 2022
More robust sign-on security is on the way, just don't expect it to arrive anytime soon.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.
CIO Business Intelligence
MARCH 15, 2022
Synthetic data defined. Synthetic data is artificially generated information that can be used in place of real historic data to train AI models when actual data sets are lacking in quality, volume, or variety. Synthetic data can also be a vital tool for enterprise AI efforts when available data doesn’t meet business needs or could create privacy issues if used to train machine learning models, test software, or the like.

Tech Republic Security
MARCH 14, 2022
A new social engineering method is spreading this malware, and it’s very easy to fall for. Here’s what it’s doing and how to avoid it. The post Cybersecurity: Attacker uses websites’ contact forms to spread BazarLoader malware appeared first on TechRepublic.

GeekWire
MARCH 17, 2022
Amazon said Thursday that its deal to acquire Hollywood studio MGM, announced in May 2021 , has closed. The $8.45 billion deal is Amazon’s second-largest acquisition behind its $13.7 billion purchase of Whole Foods in 2017. MGM will provide Amazon with more than 4,000 films and 17,000 TV shows that have collectively won more than 180 Academy Awards and 100 Emmys.
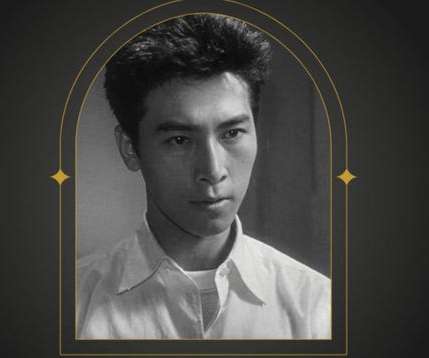
Gizmodo
MARCH 18, 2022
In Godzilla films there’s usually one star, and his name is literally the title : “Godzilla.” But actor Akira Takarada was a rare exception to the rule. Beginning with the original 1954 Toho film, Takarada became a familiar foe to the kaiju, appearing regularly over the first few decades of the franchise with multiple… Read more.

Advertisement
Start-ups & SMBs launching products quickly must bundle dashboards, reports, & self-service analytics into apps. Customers expect rapid value from your product (time-to-value), data security, and access to advanced capabilities. Traditional Business Intelligence (BI) tools can provide valuable data analysis capabilities, but they have a barrier to entry that can stop small and midsize businesses from capitalizing on them.
Let's personalize your content