20 Most Popular TechRepublic Articles in 2023
Tech Republic Security
DECEMBER 22, 2023
Here's a list of the 20 most popular articles published by TechRepublic in 2023. Read articles about ChatGPT, Google Bard, Windows 11 and more
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
DECEMBER 22, 2023
Here's a list of the 20 most popular articles published by TechRepublic in 2023. Read articles about ChatGPT, Google Bard, Windows 11 and more

Network World
DECEMBER 16, 2022
Hybrid and multicloud initiatives will continue to shape enterprise IT in 2023, and the impact on data-center networking will be felt across key areas including security, management, and operations. To read this article in full, please click here and a Network World columnist.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Network World
AUGUST 20, 2024
Attendees can expect to delve deep into the latest innovations in cloud infrastructure, applications and network security that are shaping the industry. AI will also be a major theme — from generative AI to automation to AI-driven operations and security.

Network World
AUGUST 28, 2024
Splunk, a leader in data platform and observability solutions, should enhance Cisco’s capabilities in data management, analytics and security. Other significant acquisitions by Cisco include AppDynamics in 2017 for application performance monitoring and Acacia Communications in 2021 for optical networking.

Dataconomy
NOVEMBER 21, 2023
Everything you need to know about the INL data breach 2023 is explained in this article. The Idaho National Laboratory (INL), a top-notch nuclear research hub with a knack for safeguarding national security secrets, found itself in a cyberstorm. INL data breach 2023: What happened? The critical U.S.

Flexagon
JANUARY 25, 2023
The FlexDeploy Home Page now includes popular blogs, getting started videos, and discover articles that are regularly curated and updated, providing insights to speed onboarding and learning. in February 2023. What’s Coming: 2023 Beyond FlexDeploy 6.5 With FlexDeploy 6.0 This kicks off with the delivery of FlexDeploy 6.5

SecureWorld News
JANUARY 2, 2024
In October 2023, NASA took a giant leap for all humankind. It released the Space Security: Best Practices Guide (BPG) , a landmark document designed to safeguard every satellite, communication, and mission from the lurking threats of the digital unknown. in the realm of cybersecurity.
TechSpot
AUGUST 21, 2023
Zero Day Initiative (ZDI) recently discovered a high-severity vulnerability in WinRAR, the Windows-only application developed by Eugene Roshal for managing RAR archives. Tracked as CVE-2023-40477, the bug is described as an improper validation of array index while processing recovery volumes. Read Entire Article

CIO Business Intelligence
NOVEMBER 14, 2023
billion devices reported in 2023. It also introduces new security challenges that demand our attention, especially as IoT is integrated into operational technology (OT) environments. It also introduces new security challenges that demand our attention, especially as IoT is integrated into operational technology (OT) environments.

SecureWorld News
JUNE 12, 2023
This article will provide an overview of the best cybersecurity certifications in 2023 and where you can sign up for them. Some courses are tailored to a specific discipline, while others may be broader, covering areas such as network security , ethical hacking, and more. Why are cybersecurity certifications important?
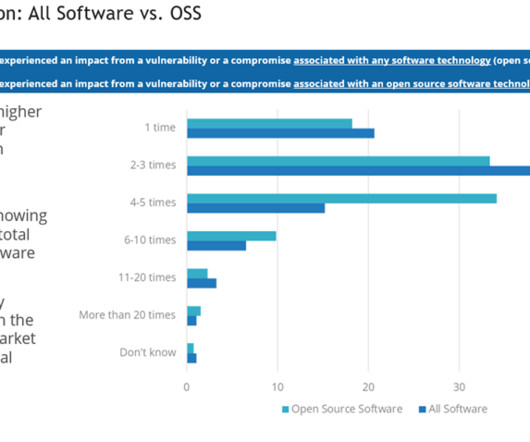
CIO Business Intelligence
AUGUST 8, 2024
Developers tend to enjoy the ability to speed application development by borrowing open source code. But there’s good news: When organizations leverage open source in a deliberate, responsible way, they can take full advantage of the benefits that open source offers while minimizing the security risks.
Dataconomy
JULY 17, 2023
The report predicts a further 16% increase in 2023, resulting in 16.7 A Statista report also suggests that the global IoT revenue is expected to reach $2,227 billion by 2028, witnessing a CAGR of 13.60% from 2023 to 2028. billion active IoT endpoints. billion connected IoT devices worldwide.

Kitaboo
DECEMBER 27, 2022
In this article, we explore the importance of sales training and how we at KITABOO can help your organization achieve its sales targets in 2023. mLearning Made Simple and Secure. And with a completely white-labeled setup, your business can deliver content via branded channels and applications without hassle.

mrc's Cup of Joe Blog
DECEMBER 20, 2022
In this article, we explore 5 challenges that CIOs and IT leaders should watch in 2023. Cyber security threats haven’t gone anywhere. In this article, we will explore some of the top challenges facing CIOs in 2023 and offer insights on how to overcome them. Keeping up with cyber-security threats. .

Kitaboo
DECEMBER 28, 2022
In this article, we explore how the right technology, be it a training management software or the training management platform you choose, can help you and your company get the most out of your training in 2023. Here are the factors you need to pay attention to when choosing your training management solution in 2023.

CIO Business Intelligence
DECEMBER 19, 2023
This year’s technology darling and other machine learning investments have already impacted digital transformation strategies in 2023 , and boards will expect CIOs to update their AI transformation strategies frequently. Meanwhile, CIOs must still reduce technical debt, modernize applications, and get cloud costs under control.

SecureWorld News
AUGUST 23, 2023
On August 8, 2023, the U.S. For a solid rundown of what the updates mean, check out this SecureWorld article from Kip Boyle , vCISO, Cyber Risk Opportunities LLC. Public Draft, as well as the related Implementation Examples draft, may be submitted to cyberframework@nist.gov by Friday, November 4, 2023. 19, Detroit on Sept.

Kitaboo
DECEMBER 22, 2022
If the ton of options across ePUB reading software intimidate you, and you are struggling to find the best ePUB reader, here’s a list of the most sought-after ePUB readers for iOS, Android, and Windows in 2023. One of the most prominent eReader applications, particularly for the ePUB file type is Adobe Digital Editions.

CIO Business Intelligence
AUGUST 23, 2023
It’s interesting how the number of projected IoT devices being connected in 2023 can differ by 26 billion from article to article. Initial visibility leads to proper segmentation for security purposes and so that users aren’t surprising you with unknown clients. You’re bound to find unknown devices on a regular basis.

SecureWorld News
JUNE 6, 2023
In the last week, a critical security flaw in Progress Software's MOVEit Transfer application came to light, exposing organizations to the risk of data breaches and potential extortion attempts. The threat actor has used similar vulnerabilities in the past to steal data & extort victims.

CIO Business Intelligence
DECEMBER 21, 2023
However, securing the cloud traffic from these workloads is a complex task, as cloud adoption increases, and the number of mission-critical workloads spread across multiple cloud providers. One of the most significant areas that organizations are revisiting is secure cloud and workload connectivity.

Scott Lowe
MAY 31, 2024
Security Matt Moore, CTO of Chainguard, goes into some detail on how Chainguard intends to honor the principles behind the CISA’s Secure by Design pledge. From my reading of the article, the greatest concern lies with untrusted networks where an attacker could manipulate things in their favor. Because…why not ?

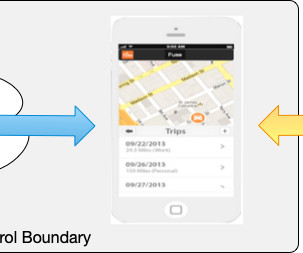
Phil Windley
MARCH 27, 2023
This article is adapted from Chapter 12 of my new book Learning Digital Identity from O'Reilly Media. I was at SLC DevOpsDays last week and attended a talk by Sharon Goldberg on MFA in 2023. I liked how she described the security provisions of passkeys (also know as Fast ID Online or FIDO). This is how they work.
CIO Business Intelligence
NOVEMBER 27, 2023
Intelligent assistants are already changing how we search, analyze information, and do everything from creating code to securing networks and writing articles. Don’t reinvent the wheel—start with a foundation model A business could invest in developing its own models for its unique applications.

Dataconomy
SEPTEMBER 29, 2023
In a digital age where security breaches are a common concern, it’s natural to question the authenticity of emails you receive, especially if they pertain to sensitive matters like payments. It was a massive breach that left millions worried about the security of their personal information. Are they real?

Dataconomy
AUGUST 15, 2023
HUB International Data Breach explained On January 17, 2023, HUB detected unusual activity within its network systems, prompting an immediate response. The findings revealed unauthorized access to certain parts of the network, with unauthorized copying of files occurring between December 2022 and January 2023.

SecureWorld News
AUGUST 7, 2023
This first installment is "Safeguarding Ethical Development in ChatGPT and Other LLMs through a Comprehensive Approach: Integrating Security, Psychological Considerations, and Governance." Three key elements require our attention: security measures, psychological considerations, and governance strategies.
Kitaboo
SEPTEMBER 12, 2023
in 2023 is set to increase to 14.1% If you feel overwhelmed with the amount of information available online, this article can help. Despite its limitations, you can open this file format in various eBook management applications. These files are created for Apple’s iBook Author (IBA) application. billion in 2027.

SecureWorld News
JUNE 24, 2024
The TRIAD Model During my career as a CISO, I relied on my TRIAD Model to envision, enact, and mobilize Information Security & Privacy strategic planning and roadmap execution activities with foundational pillars as illustrated below. I – Identity A cornerstone of a strong security and privacy program.

Scott Lowe
DECEMBER 9, 2022
This article provides a few practical examples of how using VPC Endpoints to reduce network traffic moving through NAT Gateways can help save money. Rory McCune has a series of articles on PCI compliance in containerized and Kubernetes environments. food references in the title of this article are almost too much.

ForAllSecure
MAY 19, 2023
As software development teams move towards a DevOps culture, security is becoming an increasingly important aspect of the development process. DevSecOps is a practice that integrates security into the DevOps workflow. According to GitLab’s 2022 Global DevSecOps Survey , there isn’t enough clarity around who owns security.
Scott Lowe
JANUARY 6, 2023
Welcome to Technology Short Take #163, the first of 2023! If you’re new to this site, the Technology Short Takes are essentially “link lists”—I collect links and articles about various technologies and I share them about every 3-4 weeks (sometimes more frequently). Get more details in this article.
Phil Windley
NOVEMBER 21, 2023
I recently read Igor Shadurin's article Dive Into dApps. In it, he defines a dApp (or decentralized application): The commonly accepted definition of a dApp is, in short, an application that can operate autonomously using a distributed ledger system. Let's start with the goal and work backwards from there.

Dataconomy
SEPTEMBER 29, 2023
Worse, sensitive Department of Homeland Security (DHS) information may be on the line, raising national security concerns. In this article, we’ll break down what happened, the impact on Johnson Controls and national security, and the shadowy world of Dark Angels, a hacking group pushing the boundaries of cyber warfare.

Kitaboo
AUGUST 22, 2023
In fact, in one of his articles, he said, “new open standards created in the mobile era, such as HTML5, will win on mobile devices (and on PCs too)”. Given the factors going against it, the downfall of Flash began and HTML5 emerged as a reliable and secure option for L&D professionals.

CIO Business Intelligence
DECEMBER 17, 2023
In this article, we’ll look at how AI helps companies sustain service levels at scale (during and after the holiday rush) while finding new ways to raise the bar for customer experience. In a 2023 study conducted by LivePerson , 20% of customers said they would never wait on hold and would instead opt for an AI-led conversation.

Kitaboo
FEBRUARY 16, 2024
In this article, we will explore the significance of eBook DRM protection and explore different techniques used to fortify digital assets in contemporary time. Key Features and Benefits of DRM Protection DRM protection offers a range of features and benefits designed to enhance the security of digital content. Table of Contents: I.

SecureWorld News
MAY 25, 2023
RELATED: Here's an article from The National CIO Review on "The Organizational Importance of the Chief Information Security Officer." They go through data analytics, a business application, digital applications, etc. I'm glad that I was able to be part of this one!" We call them cybersecurity champions," Chiock added.

Kitaboo
DECEMBER 19, 2023
This article aims to explore innovative approaches and cutting-edge technologies that disrupt traditional distribution channels with finesse, aiming to amplify distribution avenues and expand the market reach for published content. ’s ascent and Artificial Intelligence’s integration throughout numerous sectors.

Kitaboo
NOVEMBER 22, 2023
In this article, we will delve into the various functionalities of KITABOO that empower users to address the challenges of offline learning. Navigating the Hurdles of Offline Activity Tracking xAPI-Compliant Wrapper Applications SCORM/AICC-Compliant Wrapper Applications Applications with Preloaded Content II.

Dataconomy
JUNE 7, 2023
We will find this question’s answer in this article, but first, there is a gamer waiting to play Diablo 4, and we know how to fix it easily! net desktop application. In the Settings window, select “Update & Security.” ” From the left-hand side menu, choose “Windows Security.”

Kitaboo
MARCH 31, 2024
Native App Magazines Nowadays, many magazine publishers, such as Vogue, have created mobile applications for their publications. Their responsive design feature provides an optimized reading experience on both desktop and mobile platforms, mimicking the look and feel of contemporary websites and smartphone applications.

Dataconomy
JUNE 6, 2023
We will find this question’s answer in this article, but first, there is a gamer waiting to play Diablo 4, and we know how to fix it easily! net desktop application. In the Settings window, select “Update & Security.” ” From the left-hand side menu, choose “Windows Security.”

Kitaboo
MAY 24, 2023
This article explores the role of Digital Rights Management (DRM) in safeguarding intellectual property and discusses its benefits, challenges, and future trends. Ensuring broad compatibility without sacrificing security can be a complex task. Excessive restrictions or cumbersome processes can negatively impact user acceptance.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content