ProBeat: Net Applications will no longer track the browser wars
Venture Beast
NOVEMBER 6, 2020
After 14 years, Net Applications is killing off its NetMarketShare reports that track browser and operating system market share. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Venture Beast
NOVEMBER 6, 2020
After 14 years, Net Applications is killing off its NetMarketShare reports that track browser and operating system market share. Read More.

SecureWorld News
DECEMBER 18, 2023
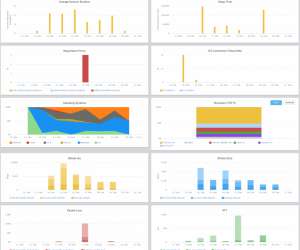
This morning, the Qualys Threat Research Unit released its 2023 Threat Landscape Year in Review report. One-third of high-risk vulnerabilities impacted network devices and web applications. This breadth showcases that no application is beyond the reach of attackers, who are determined to exploit any vulnerability to compromise systems.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

SecureWorld News
JUNE 13, 2023
Critical Start today released its biannual Cyber Intelligence Report, featuring the top threats observed in the first half of 2023 and emerging cybersecurity trends impacting the healthcare, financial services, and state and local government industries.

CIO Business Intelligence
JULY 5, 2024
A new trend — devirtualization, a process of migrating workloads from virtual to physical environments — is taking shape as a response to these changes, according to Gartner’s 2024 Hype Cycle for Data Center Infrastructure Technologies report. “On-premises So, what’s the solution?

Network World
JULY 24, 2024
Here in the Oak Ridge Leadership Computing Facility, we build leadership-class supercomputers for scientific applications,” said Matt Sieger, project director for Discovery, Oak Ridge Leadership Computing Facility (OLCF) at ORNL, which is managed and operated by UT-Battelle on behalf of the US Department of Energy.

CIO Business Intelligence
MAY 10, 2024
Data from the Dice 2024 Tech Salary Report shows that, for certain IT skills, organizations are willing to pay more to hire experts than IT pros with strong competence. NetApp Founded in 1992, NetApp offers several products using the company’s proprietary ONTAP data management operating system.

CIO Business Intelligence
FEBRUARY 12, 2024
By: Scott Sellers , Co-Founder and CEO, Azul From the get-go, the cloud promised to help companies scale up their architectures in seconds, run their applications faster, never turn away a transaction, and save money through economies of scale. Every company is different based on its industry, its available resources, and its needs.

mrc's Cup of Joe Blog
DECEMBER 19, 2019
So, where is enterprise application development headed in the coming year? photo credit: lakexyde via pixabay cc It’s an exciting time in the world of enterprise application development. These days, enterprise web application development is: Rapidly evolving : Web application development is going through major changes.
Dataconomy
MARCH 25, 2024
processors from government-operated computers and servers, thereby excluding chips manufactured by Intel and AMD, according to a report by the Financial Times. Authorities above the township level are mandated to acquire processors and operating systems deemed “safe and reliable” as per the Financial Times. and China.
CIO Business Intelligence
JULY 17, 2023
However, this shift requires a thorough understanding of the security implications and how a business can protect its data and applications. Cloud infrastructure is especially sensitive, as many critical applications are at risk, such as customer-facing applications.

CIO Business Intelligence
MAY 26, 2023
The overall perceived value of IT certifications is shifting, according to the 2023 Tech Salary Trends report from Dice. The second exam covers everything you need to know about installing and configuring operating systems, expanding security, and troubleshooting software and operational procedures.

GeekWire
MARCH 6, 2024
GeekWire reported on the company, then known as Measure Labs, in 2022. Whitehill studied deep learning algorithms for health sensing as part of the UW’s Ubiquitous Computing (UbiComp) research lab , led UW professor and health tech pioneer Shwetak Patel , who has invented several smartphone-based health applications.
The Verge
JANUARY 26, 2021
Under kernel updates, Apple notes that “a malicious application may be able to elevate privileges,” and under WebKit updates, it says “a remote attacker may be able to cause arbitrary code execution.” After both statements, the update notes say, “Apple is aware of a report that this issue may have been actively exploited.”.

CIO Business Intelligence
DECEMBER 4, 2023
By: Scott Sellers , Co-Founder and CEO, Azul After almost 30 years, Java remains the programming language of choice for large-scale enterprise applications in the cloud, on-prem, or hybrid. Its versatility, reliability, stability, and open-source and third-party libraries and frameworks make developing and running applications very efficient.

Gizmodo
JANUARY 24, 2021
ZDNet reported that the hacker group ShinyHunters, the same group who leaked millions of user records for the company that listed the “Camp Auschwitz” shirts, has dumped what appears to be data from the dating site’s user database. Millions of users of the dating site MeetMindful got some unpleasant news on Sunday. Read more.

CIO Business Intelligence
DECEMBER 5, 2023
Cyberattacks on operational technology (OT) systems are rapidly rising. In fact, manufacturing was one of the sectors most impacted by extortion attacks last year, according to Palo Alto Networks Unit 42, as reported in the 2023 Unit 42 Extortion and Ransomware Report. There are remote operations.

SecureWorld News
JULY 10, 2023
The Google Play Store, a widely-trusted source for Android applications, has recently become a battleground for a concerning wave of spyware with ties to China. Operating under the radar, these apps silently collect and transmit sensitive data to servers based in China, posing significant risks to user data security and privacy.

The Verge
JULY 26, 2021
The memory corruption issues in Apple’s desktop and mobile operating systems have been assigned the same vulnerability ID and attributed to an anonymous researcher. Impact: An application may be able to execute arbitrary code with kernel privileges. Apple is aware of a report that this issue may have been actively exploited.

mrc's Cup of Joe Blog
DECEMBER 13, 2017
So, where is enterprise application development headed in the coming year? Your organization’s ability to develop software applications for this web-based world plays a major role in your overall success. How can your business use web application development as a competitive edge? Learn more in this article.

Gizmodo
AUGUST 23, 2021
Facebook again weaseled around antitrust scrutiny in its $400 million Giphy acquisition, according to a Bloomberg report citing two sources with knowledge of the matter. If history is any indicator, Facebook can and will do whatever it wants. Read more.
Spearline Testing
JULY 7, 2022
WatchRTC collects all the relevant, useful telemetry and data points you could ever need to accurately measure your customers true experience with your application. This is done by integrating our SDK or Chrome extension with your application. Rating : Our RestAPIs can help you to get custom metrics for rating, billing and reporting.

Anoop
FEBRUARY 5, 2018
For Bulk application change or Operating system upgrade we use task sequence. User start the Task sequence from SCCM Software center and waits for content download. This delay always impacts end user self-service experience with SCCM software center. Microsoft solution to this is “SCCM Task sequence Pre-Cache Content”.

TM Forum
MARCH 10, 2022
But he adds: “Intent as a mechanism to carry requirements, build control loops and operate systems is not limited to telecoms.” ” Learning from use cases outside telecoms can help accelerate applications of autonomous systems because the needs will be very similar. TM Forum’s report.
CIO Business Intelligence
APRIL 13, 2022
Smart contracts — automatically executing transaction applications — are hosted on blockchains to simplify and secure multiparty operations. Blockchain-based applications are already helping to boost Africa’s socio-economic development and operational systems, according to the African Union Development Agency in a recent report.

SecureWorld News
OCTOBER 25, 2022
As is usually the case with actively exploited Zero-Day flaws, Apple refrained from sharing more specifics about the shortcoming other than acknowledging that it's "aware of a report that this issue may have been actively exploited.". CVE-2022-22675 : An application may be able to execute arbitrary code with kernel privileges.

CIO Business Intelligence
JANUARY 4, 2024
The CCA allows overarching enterprise functions and IT shared services to be assessed separately from the business unit’s products/applications that require PCI security compliance. Simplified reporting When it comes to PCI security compliance, reporting can be a time-consuming and intricate task.
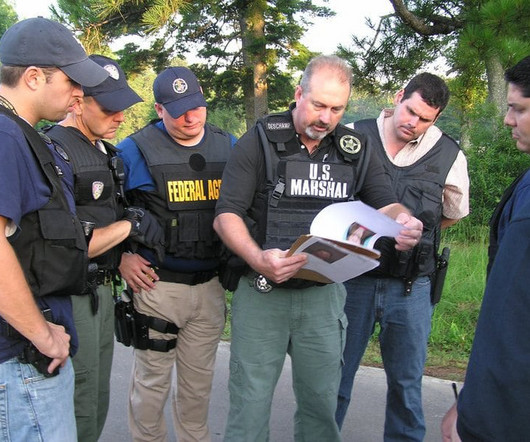
SecureWorld News
FEBRUARY 28, 2023
The hackers also encrypted some files on the system and demanded a ransom for their decryption, according to reports from NBC News and Reuters. The USMS is investigating the incident with assistance from other federal agencies, such as the FBI and DHS.

CIO Business Intelligence
JUNE 8, 2023
There’s a strong need for workers with expertise in helping companies make sense of data, launch cloud strategies, build applications, and improve the overall user experience. Systems engineer For organizations running complex hardware, software, and network systems, the role of a systems engineer is a vital part of daily operations.

SecureWorld News
DECEMBER 6, 2022
A report from Kaspersky says that CryWiper disguises itself as ransomware so that it can extort money from the victim for decrypting the data, but in reality, it intentionally destroys data in the affected systems. Read the original report, New Trojan CryWiper pretends to be a ransomware , for more information.

TM Forum
DECEMBER 1, 2022
Developers also have access to free network APIs, such as device location, diagnostic tools, and SMS notifications, and an SDK based on the Zephyr Real-time Operating System. As Fierce Wireless reported. , it will show how eight software vendors use the APIs to create new applications. IoT outliers. Developer Hub website.

CIO Business Intelligence
NOVEMBER 6, 2023
To ensure the security of your cloud applications, infrastructure, and operating systems, it’s important to schedule regular vulnerability scans and penetration tests. It is also crucial to promptly apply patches and updates to protect your systems against known risks. Adopt the use of passphrases instead of passwords.

The Verge
JANUARY 12, 2022
version of iOS, a minor update to the mobile operating system that fixes bugs, including a denial-of-service vulnerability previously reported by The Verge. patch addresses a vulnerability triggered through HomeKit, the software API for connecting smart home devices to iOS applications.

CIO Business Intelligence
OCTOBER 4, 2023
A volatile market Over 28% of skills and certifications changed in market value from April 1 through July 1 (the period covered by Foote Partners’ Q3 report), a far greater number than the 19% quarterly average over the last 24 months. While 159 rose in value, 205 declined, compared to 124 rising and 159 declining in the previous quarter.

CIO Business Intelligence
SEPTEMBER 19, 2023
To gain a better understanding of how companies are putting AI to practical use, consultancy Deloitte surveyed 2,620 global business leaders, across 13 countries, as part of its Fueling the AI Transformation report. IT operations management AI IT operations management ( AIOps ) tools are growing in popularity.

SecureWorld News
JUNE 1, 2023
Microsoft promptly reported the issue to Apple, resulting in the release of security updates to address the vulnerability. Understanding System Integrity Protection (SIP) System Integrity Protection, also known as "rootless," is a fundamental macOS security feature introduced by Apple in macOS Yosemite.

SecureWorld News
AUGUST 10, 2020
Microsoft and other industry professionals strongly recommend upgrading computer systems to an actively supported operating system.". When an operating system reaches its End of Life, it becomes a prime target for hackers. An unsupported operating system grants hackers easier pickings.

Hacker Earth
JANUARY 16, 2024
It continues to be a top choice for building robust and versatile applications. Java has been a robust and versatile programming language with a strong ecosystem, widely used in enterprise-level applications. Clearly, JavaScript remains the backbone of dynamic and interactive web applications.

Go Hire- IT
SEPTEMBER 8, 2023
The Best Recruitment Tips from Microsoft, Nvidia, and EssilorLuxottica (image source) A previous report discussed Pets Gone Wild Resort, a small business based in Pasadena, Texas, which has garnered mixed reactions for its peculiar sign that reads, “Now Hiring: Non Stupid People.”

CTOvision
JUNE 7, 2014
These are examples of consumer-oriented sensors and devices, but that has occurred in parallel with business, professional, infrastructure, government and military applications. Pacemakers can report statistics on your heart to doctors and hospitals. weather reports). Here are some examples….

CIO Business Intelligence
MARCH 11, 2024
It will improve project management, help with requirements creation, assist developers with coding, cover the system with auto-tests, report defects, and improve deployment. According to Deloitte research , AI will boost the productivity of software development processes from 50% to 1000%.

Linux Academy
FEBRUARY 25, 2019
When we think of patching, we most often think of patching our servers and workstations operating systems, but we can’t stop there. Well, there’s all of your network devices, IoT devices, hypervisors, and let’s not forget about all of those wonderful applications! These types of applications must be patched as well.

Dataconomy
OCTOBER 17, 2023
These individuals use the same techniques as malicious hackers, but instead of using them for nefarious purposes, they use them to identify vulnerabilities and weaknesses in an organization’s systems, networks, and applications. They may steal sensitive data, disrupt systems, or engage in other illicit activities.

Network World
JULY 22, 2016
Earlier this year, Cisco’s Talos division reported significant image-processing bugs to Apple , one of which could allow attackers to inject malware or remotely execute code via “iMessages, malicious webpages, MMS messages, or other malicious file attachments opened by any application.”

Cloud Musings
JUNE 29, 2017
Did you know that the reservations systems of the biggest carriers mostly run on a specialized IBM operating system known as Transaction Processing Facility (TPF). With all the major technologies changes since then, it’s clear that IBM has already accomplished a herculean task by keeping an application viable for over 50 years!
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content