Are Your Firewalls and VPNs the Weakest Link in Your Security Stack?
Network World
OCTOBER 21, 2024
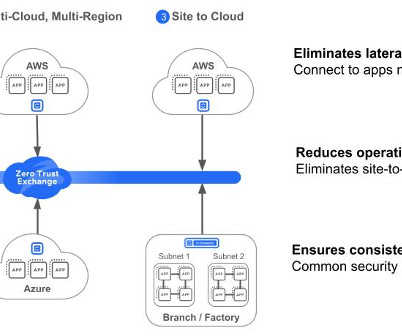
It’s the opposite of a firewall and VPN architecture, where once on the corporate network everyone and everything is trusted. A Zero Trust platform ensures applications and data are not visible to the public internet and users are only provided least privilege access, preventing lateral movement and protecting against ransomware attacks.















































Let's personalize your content