How to enable 2FA for groups in Nextcloud
Tech Republic Security
APRIL 6, 2020
Nextcloud allows you to enforce groups to use two-factor authentication. Let's find out how to create a group and then add them to 2FA enforcement.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Tech Republic Security
APRIL 6, 2020
Nextcloud allows you to enforce groups to use two-factor authentication. Let's find out how to create a group and then add them to 2FA enforcement.

Tech Republic Security
MARCH 23, 2022
The Lapsus$ cybercriminal group exposed screenshots and messages showing it had successfully breached identify platform Okta. The post Okta authentication company’s customer data targeted by the Lapsus$ gang appeared first on TechRepublic. Read about it and see how to protect yourself from this threat.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CIO Business Intelligence
MARCH 4, 2025
Researchers at the firm also identified seven new Chinese-origin cyber espionage groups in 2024, many of which exhibited specialized targeting and toolsets. The report also highlighted that Chinese groups continue to share malware tools a long-standing hallmark of Chinese cyber espionage with the KEYPLUG backdoor serving as a prime example.

Network World
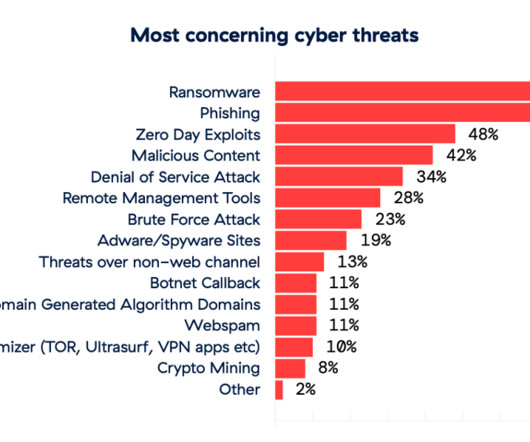
OCTOBER 11, 2024
End-user organizations have their part in the blame for this, said Jeremy Roberts, senior research director at Info-Tech Research Group, and unconnected with the study. This situation is in part down to human nature, according to Scott Young, principal advisory director at Info-Tech Research Group.

Tech Republic Security
MARCH 27, 2020
Nextcloud allows you to enforce groups to use two-factor authentication. Let's find out how to create a group and then add them to 2FA enforcement.

Network World
JANUARY 21, 2025
For example, it is role oriented, which will allow cluster operators to define how shared infrastructure can be used by many different groups, Ferreira noted. That said, Ferreira argued that the Gateway API is much more than just a new ingress controller standard. The Gateway API also has more expressiveness, according to Ferreira.

Tech Republic Security
SEPTEMBER 21, 2022
The post Uber exposes Lapsus$ extortion group for security breach appeared first on TechRepublic. In last week’s security breach against Uber, the attackers downloaded internal messages from Slack as well as information from a tool used to manage invoices.

CIO Business Intelligence
MARCH 4, 2025
Researchers at the firm also identified seven new Chinese-origin cyber espionage groups in 2024, many of which exhibited specialized targeting and toolsets. The report also highlighted that Chinese groups continue to share malware tools a long-standing hallmark of Chinese cyber espionage with the KEYPLUG backdoor serving as a prime example.

CIO Business Intelligence
OCTOBER 17, 2024
A cursory check and balance on the name of the certifying authority will help to know the likely authenticity of the certification claim,” said Abhishek Gupta, CIO at leading Indian satellite broadcaster DishTV. The certification authenticity forms a smaller part of overall final decision-making, said Gupta.

Network World
FEBRUARY 10, 2025
In 2023, Notre Dame began working with PIER Group, an Indiana-based technology service provider focused on education and research markets, to design, plan and implement the Wi-Fi upgrade. Teamwork is key Buysse credits PIER Group with helping to get the project over the goal line. The planning and strategizing phase took about a year.

Network World
MARCH 31, 2021
Cisco made enhancements to its security offerings that will expand and change the way customers buy its Secure Access Service Edge products as well as bolster network-access authentication.

CIO Business Intelligence
MAY 19, 2022
Customer demand for passwordless authentication has grown exponentially since smartphones first began offering built-in biometric readers. A staggering 93% of consumers preferred biometric authentication to passwords — and yet so many companies still force their customers to use risky, outdated login credentials. Your first clue?

Network World
APRIL 24, 2023
The service can also onboard new devices, authenticate existing users, segment devices on the network, or help troubleshoot problems from a cloud-based system, according to Pramod Badjate, group vice president and general manager, of Arista’s Cognitive Campus group. To read this article in full, please click here

Tech Republic Security
JANUARY 21, 2025
The phishing-as-a-service kit from Sneaky Log creates fake authentication pages to farm account information, including two-factor security codes.

CIO Business Intelligence
MARCH 31, 2025
PM Ramdas, CTO & Head Cyber Security, Reliance Group adds, Organizations need complete visibility into security tool decisions that protect enterprise infrastructure. We also employ adaptive authentication, such as liveness detection, contextual MFA, and real-time identity challenges, to thwart impersonation attempts.

Anoop
SEPTEMBER 19, 2022
The post New Windows 11 Configure Hash Algorithms for Certificate Logon Authentication Group Policy for Kerberos appeared first on HTMD Community Blog #1 Modern Device Management Guides by Anoop C Nair. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates.

Network World
FEBRUARY 10, 2025
Now you can take that signal and just carry it through and thats why theres an efficiency there, says Jimmy Yu, an analyst at the DellOro Group. For example, earlier this year, the company added two-factor authentication for customer portals. The biggest savings for them is they get fewer support tickets to their IT help desk, he says.

CIO Business Intelligence
NOVEMBER 26, 2024
For example, a financial services firm adopted a zero trust security model to ensure that every access request is authenticated and authorized. IDC is a wholly owned subsidiary of International Data Group (IDG Inc.), the world’s leading tech media, data, and marketing services company. Contact us today to learn more.

CIO Business Intelligence
JULY 29, 2022
For financial services company Capital Group, competing in tight IT talent markets is all about the long run. “We That focus includes not only the firm’s customer-facing strategies but also its commitment to investing in the development of its employees, a strategy that is paying off, as evidenced by Capital Group’s No. Capital Group.

SecureWorld News
FEBRUARY 26, 2025
With investigators rapidly tracing the digital breadcrumbs, several experts have now pointed to North Korea's notorious Lazarus Group as the likely culprit behind the audacious breach. Dubai-based exchange Bybit was targeted in a malware-driven attack that resulted in the theft of approximately $1.46 billion in crypto assets.

CIO Business Intelligence
MARCH 14, 2025
Also concerning is the rise of hacktivist groups that target vulnerable groups and networks on behalf of state actors to create ideological differences and public mistrust. Multi-factor authentication (MFA) should no longer be optional, especially as BYOD has become the norm.
Network World
JANUARY 23, 2025
Zscaler ThreatLabz 2024 Ransomware Report disclosed a record-breaking ransom payment of $75 million to Dark Angles, a ransomware group, last year. This is substantiated by Zscalers research wing, ThreatLabz, which determined that ransomware attacks will become more advanced and persistent.

CIO Business Intelligence
JANUARY 24, 2025
By bringing different core technologies together, this data orchestration hub removes the need for this authentication because the different core technologies are connected. If you send money from your bank account to someone at another bank, theres a delay as the other bank verifies the funds.

SecureWorld News
FEBRUARY 3, 2025
Dubbed Operation Heart Blocker, the coordinated effort targeted a cybercriminal group known as Saim Raza, also operating under the name HeartSender. For every criminal group disrupted, multiple others remain active or emerge to take their place." According to the U.S.

Network World
SEPTEMBER 18, 2024
A cybersecurity red team acts as a group of ethical hackers who simulate infrastructure attacks to identify weaknesses and vulnerabilities that malicious actors could exploit. The importance of strong authentication: Another key area that red teams focus on is authentication.

CIO Business Intelligence
OCTOBER 10, 2023
Foster adaptability and flexibility Adaptable work environments and agile methodologies form the bedrock of a thriving IT culture, says Charman Hayes, executive vice president of people and capability for the technology group at Mastercard. Secure funding, design a program for a small group of individuals, and run a pilot,” he advises.

CIO Business Intelligence
FEBRUARY 18, 2025
Mistral believes that LLMs that are custom-trained in regional languages can help service these use cases as the custom training would help an LLM grasp the unique intricacies and insights for delivering precision and authenticity. We have been observing that language-specific LLMs have been growing in the Middle East.

Network World
FEBRUARY 13, 2025
Market research firm DellOro group forecasts that the SASE market will triple by 2026 , topping $13 billion. The security features of SASE can include encryption, multifactor authentication, threat protection, data leak prevention (DLP), DNS, Firewall-as-a-Service ( FWaaS ), Secure Web Gateway (SWG), and Zero Trust Network Access (ZTNA).

CIO Business Intelligence
MARCH 13, 2025
I want to be authentic. Working for people like Kristin [Peck, CEO of Zoetis] and all the other wonderful women leaders we have has made me realize how genuinely authentic and comfortable they are. Ptacek, who says her peer group cohort still meets weekly, likens it to a board of directors outside of your company circle.

Network World
MARCH 23, 2017
A group of hackers threatening to wipe data from Apple devices attached to millions of iCloud accounts didn't obtain whatever log-in credentials they have through a breach of the company's services, Apple said. The alleged list of email addresses and passwords appears to have been obtained from previously compromised third-party services."

CIO Business Intelligence
AUGUST 29, 2024
Unlike traditional one-time passwords (OTPs), which have become increasingly vulnerable to phishing, SIM swapping, and message interception, payment passkeys utilize biometric data stored on a user’s device to authenticate transactions.

Network World
SEPTEMBER 19, 2024
Juniper joins a group of vendors offering Wi-Fi 7 products, however general enterprise use of Wi-Fi 7 is still likely a couple years off. Additional features such as encryption and authentication over WPA3 Enterprise further strengthen Wi-Fi security. What’s going on with Wi-Fi 7?

CIO Business Intelligence
MARCH 31, 2025
Additionally, PAM prevents unauthorized access by enforcing least privilege and multi-factor authentication and by only provisioning elevated permissions temporarily. PAM should vault away all accounts that are members of the Domain Administrators group and establish a checkout/check-in process for them.

CIO Business Intelligence
JANUARY 22, 2025
In general, mastering the art of meaningful 1:1 conversation can help create a peer group around you that can provide counsel, truth bombs or encouragement as you embark on the journey to be the kind of leader you want to be. Ive found incredible value in hearing someone authentically share their experiences from all levels.

SecureWorld News
NOVEMBER 22, 2024
The United States Department of Justice (DOJ) has unsealed charges against five individuals accused of orchestrating sophisticated phishing campaigns tied to the notorious Scattered Spider cybercrime group.

IT Toolbox
JULY 13, 2023
China’s Storm-0558 compromised 25 email accounts belonging to government officials by forging authentication tokens. The post Chinese Cyberespionage Group Compromises U.S. and European Gov Emails, Threat Mitigated appeared first on Spiceworks.

CIO Business Intelligence
OCTOBER 16, 2023
Okta issued an alert to clients in late August warning about incoming threats by hackers to gain access to “manipulate the delegated authentication flow via Active Directory (AD) before calling the IT service desk at a targeted organization, requesting a reset of all MFA factors in the target account.” Ransomware, Security
CIO Business Intelligence
OCTOBER 25, 2023
This formidable threat group poses significant challenges to telecommunications, technology and software automation industries. Muddled Libra has a signature move: exploit the 0ktapus phishing kit to craft believable authentication pages and manipulate victims through social engineering. Tune in and stay updated.

CIO Business Intelligence
AUGUST 29, 2024
When you add multi-factor authentication (MFA) resets to the picture, that number is likely even higher. Most authentication methods are actually quite easy to get around, and in many cases were never intended to be security factors. But what happens when a user can’t access their authenticator app?

CIO Business Intelligence
OCTOBER 25, 2023
Reconnaissance Uses AD explorer to enumerate users, computers, and groups. Creates decoy users, user groups, and computers in your Active Directory. Use FIDO2-Based MFA : FIDO2 (Fast Identity Online) is a strong authentication standard that provides secure and passwordless authentication.

SecureWorld News
FEBRUARY 15, 2024
A sophisticated form of mobile malware dubbed "GoldPickaxe" has been uncovered, which collects facial recognition data to produce deepfake videos, enabling hackers to bypass biometric authentication protections on banking apps. Experts warn that biometric authentication alone is not foolproof.

Network World
SEPTEMBER 12, 2024
NIST, other government agencies, and industry bodies point towards the policy enforcement point (PEP) as the gateway device or service that performs this separation, gating access based on different authentication and authorization requirements, depending on the sensitivity of the resource.
CIO Business Intelligence
OCTOBER 25, 2023
Regan and David Moulton, discuss the challenges Muddled Libra and other threat groups pose. Stronger multifactor authentication (MFA) methods and secure VPNs are critical components in defense. Threat actors are often highly persistent and can rapidly pivot when encountering roadblocks.

CIO Business Intelligence
FEBRUARY 3, 2025
A concept that resonates with Rebecca Fox, CIO of NCC Group, is grip and control, an expression coined by Apple founder Steve Jobs, which means that every time you adjust your grip on a phone, you risk dropping it. Transparency and adaptability should be a core part of how digital leaders lead. one wants stereo instructions.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content