Tempered Networks simplifies secure network connectivity and microsegmentation
Network World
JULY 1, 2019
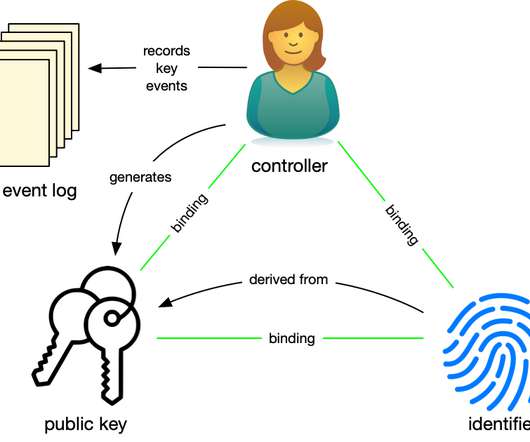
The TCP/IP protocol is the foundation of the internet and pretty much every single network out there. There’s nothing in the protocol for security, mobility, or trusted authentication. This dual functionality of the address lacks the basic mechanisms for security and mobility of devices on a network.


















































Let's personalize your content