No, the Cloud Is Not a Green Technology
Information Week
FEBRUARY 28, 2022
Since the cloud is nothing more than a rented data center that someone else owns, cloud computing itself can't be much greener than any other data center technology.

Information Week
FEBRUARY 28, 2022
Since the cloud is nothing more than a rented data center that someone else owns, cloud computing itself can't be much greener than any other data center technology.

Association of Information Technology Professional
FEBRUARY 9, 2022
Being on the forefront of technology now includes effective policies around data management and analytics.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Social, Agile and Transformation
FEBRUARY 17, 2022
Intelligent search powers ecommerce websites, site search engines, portals to support hybrid working, and customer support workflows. We’re going from the early days of keyword search boxes to today’s natural language query interfaces. The intelligence will progress from today’s automatic relevance tuning machine learning algorithms onto tomorrow’s pre-trained models and program.

Forrester IT
FEBRUARY 28, 2022
CISOs and their teams in Europe and worldwide are either already experiencing cybersecurity impacts from the war in Ukraine and the sanctions imposed on Russian and Belarusian actors – or they soon will. If you haven’t already, here are the cybersecurity-related steps to take right now, plus some pitfalls to avoid: At the risk of […].

Advertiser: ZoomInfo
Sales and marketing leaders have reached a tipping point when it comes to using intent data — and they’re not looking back. More than half of all B2B marketers are already using intent data to increase sales, and Gartner predicts this figure will grow to 70 percent. The reason is clear: intent can provide you with massive amounts of data that reveal sales opportunities earlier than ever before.

The Accidental Successful CIO
FEBRUARY 2, 2022
Which software development methodology is best? Image Credit: Silver Blu3. As a CIO I suspect that you are well aware that there are a number of different ways that your IT teams can go about developing software (and doing a lot of other things). There is the classic method that has been used for over 40 years called “waterfall” Then there’s the new upstart in town that everyone seems to be flocking to called “agile” All of these options can place a CIO in a difficu
Anoop
FEBRUARY 23, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post SCCM CMPivot query to check Windows 11 Compatibility appeared first on HTMD Blog #1 by Anoop C Nair.
Information Technology Zone brings together the best content for IT professionals from the widest variety of industry thought leaders.

Association of Information Technology Professional
FEBRUARY 11, 2022
Learn 4 Linux and Windows commands to display IP address settings for network configuration and troubleshooting.

Social, Agile and Transformation
FEBRUARY 7, 2022
I ask this question to agile leaders working with five or more teams: What boundaries and empowerments do you set for your self-organizing teams? . More specifically, are their agile teams free to choose their own tools and technologies? Can the scrum masters lead agile backlogs the way that worked for them at one of their previous jobs?

Forrester IT
FEBRUARY 28, 2022
Risk management leaders in Europe and worldwide are already being impacted by the war in Ukraine and the sanctions imposed on Russian and Belarusian actors. Forrester analysts provide their guidance in this post.

Tech Republic Security
FEBRUARY 18, 2022
Corporate users are more aware of phishing attacks in their mailboxes. Yet they are not used to being targeted via other systems like Microsoft Teams. Learn how to protect yourself. The post Cyberattack threat: Corporate users infected via Microsoft Teams appeared first on TechRepublic.

Advertiser: GEP
For years, you and your team have fought an uphill battle. Supply disruptions. Cost pressures. ESG compliance. You name it, and you’ve had to navigate it. In 2025, many challenges will persist, but procurement and supply chain teams have a powerful tool with rapidly advancing capabilities to tackle them — artificial intelligence (AI). The GEP Outlook 2025 report examines the disruptive transformation AI is driving in procurement and supply chains, alongside other key trends and the macroeconomic

Anoop
FEBRUARY 16, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post Windows 365 Cloud PC Azure AD Joined Provisioning Process appeared first on HTMD Blog #1 by Jitesh Kumar.

Information Week
FEBRUARY 11, 2022
Automation is helping accelerate business processes and organizations. For those looking to land a job in IT automation, a long list of IT skills can be applied.

Association of Information Technology Professional
FEBRUARY 18, 2022
If you enjoy collecting data and using statistical methods to guide decision making, operations analyst could be your next move.

Network World
FEBRUARY 25, 2022
2022 will be another busy year for enterprise incident responders as ransomware, supply chain and myriad zero-day attacks will continue to rise, according to Cisco's Talos security experts. To help address the threats, the Cisco Talos team used a blog and online presentation to detail steps enterprises can take to defend themselves against the growing field of bad actors and also to point out lessons learned from recent damaging exploits such as the Log4j vulnerability and Microsoft Exchange ser

Speaker: Carolyn Clark and Miriam Connaughton
Forget predictions, let’s focus on priorities for the year and explore how to supercharge your employee experience. Join Miriam Connaughton and Carolyn Clark as they discuss key HR trends for 2025—and how to turn them into actionable strategies for your organization. In this dynamic webinar, our esteemed speakers will share expert insights and practical tips to help your employee experience adapt and thrive.

Forrester IT
FEBRUARY 23, 2022
The most successful companies put their customers at the heart of all they do. Yet customer obsession is not an all-or-nothing proposition.

Tech Republic Security
FEBRUARY 25, 2022
The conflict we all feared is expected to bring an increase of cyberattacks, but experts agree that all hope isn’t lost. The post How Russia’s invasion of Ukraine will affect your cybersecurity appeared first on TechRepublic.

Anoop
FEBRUARY 18, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post Configure Enterprise Mode Site List to Use IE Mode Using Intune appeared first on HTMD Blog #1 by Jitesh Kumar.

Information Week
FEBRUARY 25, 2022
In 2020, the Department of Defense created a data management vision that any enterprise would do well to emulate.

Advertisement
Large enterprises face unique challenges in optimizing their Business Intelligence (BI) output due to the sheer scale and complexity of their operations. Unlike smaller organizations, where basic BI features and simple dashboards might suffice, enterprises must manage vast amounts of data from diverse sources. What are the top modern BI use cases for enterprise businesses to help you get a leg up on the competition?

Association of Information Technology Professional
FEBRUARY 21, 2022
Now more than ever, online training has become essential for gaining IT skills.

All Things Distributed
FEBRUARY 22, 2022
Diving into Quantum computing with Prof.

Forrester IT
FEBRUARY 14, 2022
Politicians of all persuasions will agree that people make decisions in strange ways. The motivations of voters are complex. Political campaign managers must understand this complexity in order to target the right likely voters with the right message at the right time. To do this, they often break the electorate into three broad groups based […].

Tech Republic Security
FEBRUARY 11, 2022
The federal agency says hundreds of victims have lost money due to scams over a two-year span. The post FBI: Criminals escalating SIM swap attacks to steal millions of dollars appeared first on TechRepublic.

Advertiser: Procom Services
Procom’s 2024 Salary Guide provides critical insights into the latest hiring trends, in-demand IT roles, and competitive pay rates across Canada and the U.S. It highlights key market dynamics such as the growing demand for remote work, skills-based hiring, and flexible staffing solutions. With detailed pay rate data for top IT positions like Cybersecurity Consultants, Cloud Engineers, and Salesforce Developers, this guide is an essential resource for companies looking to stay competitive in toda

Anoop
FEBRUARY 14, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post How to Install SCCM Client using Intune for Autopilot Provisioned Devices appeared first on HTMD Blog #1 by Kannan CS.

Information Week
FEBRUARY 22, 2022
The answer for IT and business leaders facing exodus: Focus on product-led growth to limit the impact of talent departure and team productivity.

Association of Information Technology Professional
FEBRUARY 4, 2022
Learn how SD-WAN and SASE can complement one another to design a network with more contextual intelligence and central policy management.

Tech Republic Cloud
FEBRUARY 24, 2022
To spot faults quickly even if they take a month to show up, Azure feeds signals into a machine learning system: in the future, you will be able to do that for your own cloud workloads. The post Machine learning: The AIOps system Azure uses to make the cloud reliable appeared first on TechRepublic.

Advertisement
For many IT admins, business as usual is a juggling act. Job schedulers and scripts run on autopilot, applications and operating systems can’t speak the same language, and other tools—like RPA or MFT solutions—operate in isolation. On a good day, everything runs smoothly. But good days are rare; more often than not, something goes wrong and you’re stuck putting out fires.

Forrester IT
FEBRUARY 9, 2022
Onboard New Reps Fast To Avoid Missing Out On Revenue Onboarding new reps quickly is key to achieving annual revenue and quota goals. To do this, sales executives should develop a best-in-class onboarding program by utilizing three core principles: Establish what the sales organization will do to help reps gain competencies. Outline what the new […].

Tech Republic Security
FEBRUARY 24, 2022
Whether the chicken or the egg came first, Beyond Identity’s data suggests that the fastest growing companies are all more likely to take cybersecurity seriously. The post What hyper-growth companies all have in common: They prioritize cybersecurity appeared first on TechRepublic.
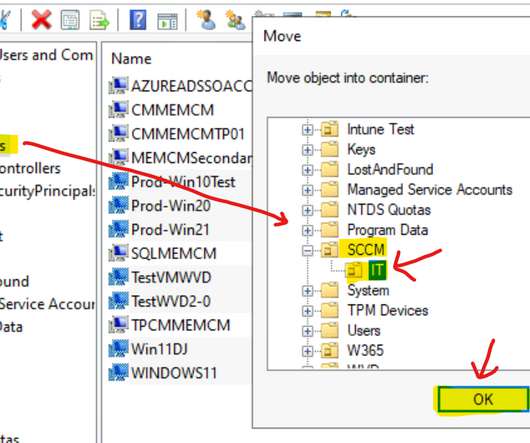
Anoop
FEBRUARY 21, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post SCCM Collection based on Active Directory OU | The Easy Way appeared first on HTMD Blog #1 by Anoop C Nair.

Information Week
FEBRUARY 22, 2022
When people can work from anywhere, where do they choose to live? The answers might surprise you.

Advertiser: ZoomInfo
In this exploration, we're diving into predictions about the future of sales. We're talking about a complete shake-up powered by automation and artificial intelligence (AI). These aren't just fancy tools — they're real game-changers. Automation and AI are here to redefine every interaction, making them smarter, faster, and more meaningful. From personalized customer journeys to streamlined sales processes, the goal is to make every moment count, enhancing both efficiency and connection.
Let's personalize your content