No, the Cloud Is Not a Green Technology
Information Week
FEBRUARY 28, 2022
Since the cloud is nothing more than a rented data center that someone else owns, cloud computing itself can't be much greener than any other data center technology.

Information Week
FEBRUARY 28, 2022
Since the cloud is nothing more than a rented data center that someone else owns, cloud computing itself can't be much greener than any other data center technology.

Association of Information Technology Professional
FEBRUARY 9, 2022
Being on the forefront of technology now includes effective policies around data management and analytics.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Anoop
FEBRUARY 23, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post SCCM CMPivot query to check Windows 11 Compatibility appeared first on HTMD Blog #1 by Anoop C Nair.

Tech Republic Security
FEBRUARY 18, 2022
Corporate users are more aware of phishing attacks in their mailboxes. Yet they are not used to being targeted via other systems like Microsoft Teams. Learn how to protect yourself. The post Cyberattack threat: Corporate users infected via Microsoft Teams appeared first on TechRepublic.

Advertisement
Large enterprises face unique challenges in optimizing their Business Intelligence (BI) output due to the sheer scale and complexity of their operations. Unlike smaller organizations, where basic BI features and simple dashboards might suffice, enterprises must manage vast amounts of data from diverse sources. What are the top modern BI use cases for enterprise businesses to help you get a leg up on the competition?

Network World
FEBRUARY 25, 2022
2022 will be another busy year for enterprise incident responders as ransomware, supply chain and myriad zero-day attacks will continue to rise, according to Cisco's Talos security experts. To help address the threats, the Cisco Talos team used a blog and online presentation to detail steps enterprises can take to defend themselves against the growing field of bad actors and also to point out lessons learned from recent damaging exploits such as the Log4j vulnerability and Microsoft Exchange ser

Tech Republic Cloud
FEBRUARY 24, 2022
To spot faults quickly even if they take a month to show up, Azure feeds signals into a machine learning system: in the future, you will be able to do that for your own cloud workloads. The post Machine learning: The AIOps system Azure uses to make the cloud reliable appeared first on TechRepublic.
Information Technology Zone brings together the best content for IT professionals from the widest variety of industry thought leaders.

GeekWire
FEBRUARY 28, 2022
Microsoft CEO Satya Nadella and his wife Anu Nadella, photographed with their son, Zain. (Photo courtesy Microsoft and Seattle Children’s). Zain Nadella, the son of Microsoft CEO Satya Nadella and his wife, Anu Nadella, died Monday at the age of 26, according to a message sent to the company’s executives. “Zain will be remembered for his eclectic taste in music, his bright sunny smile and the immense joy he brought to his family and all those who loved him,” wrote Jeff Sp

Anoop
FEBRUARY 16, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post Windows 365 Cloud PC Azure AD Joined Provisioning Process appeared first on HTMD Blog #1 by Jitesh Kumar.

Tech Republic Security
FEBRUARY 11, 2022
The federal agency says hundreds of victims have lost money due to scams over a two-year span. The post FBI: Criminals escalating SIM swap attacks to steal millions of dollars appeared first on TechRepublic.

Network World
FEBRUARY 1, 2022
Research firm Gartner forecasts IT spending will reach nearly $4.5 trillion worldwide this year, with enterprise software, IT services, and data center systems leading the way. The projected $4.45 trillion in spending this year represents an increase of 5.1% compared with 2021. The largest growth segment is enterprise software, which is projected to grow 11% to $672 billion.

Advertiser: Procom Services
Procom’s 2024 Salary Guide provides critical insights into the latest hiring trends, in-demand IT roles, and competitive pay rates across Canada and the U.S. It highlights key market dynamics such as the growing demand for remote work, skills-based hiring, and flexible staffing solutions. With detailed pay rate data for top IT positions like Cybersecurity Consultants, Cloud Engineers, and Salesforce Developers, this guide is an essential resource for companies looking to stay competitive in toda

The Verge
FEBRUARY 26, 2022
Illustration by Alex Castro / The Verge. As the invasion of Ukraine enters its third day, Russia has blocked access to Twitter in an apparent effort to stifle the flow of information, according to a report from the internet monitoring group NetBlocks. Beginning Saturday morning, NetBlocks saw failed or heavily throttled connections across every major Russian telecom provider, including Rostelecom, MTS, Beeline, and MegaFon.

Information Week
FEBRUARY 4, 2022
Amid massive supply chain disruptions, companies are increasingly prioritizing sustainability and circularity to eliminate ‘take, make, waste’ and support better agility.

Gizmodo
FEBRUARY 24, 2022
IDW’s Teenage Mutant Ninja Turtles comic series has taken the titular heroes and their half-shells on some wild adventures, playing with established TMNT canon in some fascinating ways. Now, their current story is going to include a major shock to the system: the return of a controversial, major figure from the team’s… Read more.

Anoop
FEBRUARY 18, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post Configure Enterprise Mode Site List to Use IE Mode Using Intune appeared first on HTMD Blog #1 by Jitesh Kumar.

Advertisement
For many IT admins, business as usual is a juggling act. Job schedulers and scripts run on autopilot, applications and operating systems can’t speak the same language, and other tools—like RPA or MFT solutions—operate in isolation. On a good day, everything runs smoothly. But good days are rare; more often than not, something goes wrong and you’re stuck putting out fires.

Tech Republic Security
FEBRUARY 25, 2022
The conflict we all feared is expected to bring an increase of cyberattacks, but experts agree that all hope isn’t lost. The post How Russia’s invasion of Ukraine will affect your cybersecurity appeared first on TechRepublic.
Network World
FEBRUARY 8, 2022
Security firm Binarly has discovered more than 20 vulnerabilities hiding in BIOS/UEFI software from a wide range of system vendors, including Intel, Microsoft, Lenovo, Dell, Fujitsu, HP, HPE, Siemens, and Bull Atos. Binarly found the issues were associated with the use of InsydeH20, a framework code used to build motherboard unified extensible firmware interfaces (UEFI), the interface between a computer’s operating system and firmware.

GeekWire
FEBRUARY 25, 2022
Rally in support of Ukraine at the University of Washington Thursday. (GeekWire Photo | Charlotte Schubert). As disinformation and Russian propaganda flood social media during the invasion of Ukraine, information experts are providing advice about how avoid propagating false narratives. Kate Starbird , director of the University of Washington’s Center for an Informed Public (CIP), shared her views in a series of tweets Thursday.

Information Week
FEBRUARY 11, 2022
It’s essential for IT professionals to recognize and internalize the importance of writing skills in the changing world of remote and hybrid work environments.

Speaker: Miriam Connaughton and Donald Knight
As organizations scale, keeping employees connected, engaged, and productive can seem like a monumental task. But what if AI could help you do all of this and more? AI has the power to help, but the key is implementing it in a way that enhances, rather than replaces, human connection. Join us for an exploration into how industry trailblazers are using AI to transform employee experience at scale while addressing both the potential and the pitfalls.

Gizmodo
FEBRUARY 11, 2022
The long saga of the union—and separation —of Marvel and Netflix’s shared superhero streaming ambitions is reaching a peculiar end , it seems. Quietly, Netflix has revealed that all six of its original Marvel streaming series will join a rare handful of Netflix Originals to leave the service, and it’s not sure yet if,… Read more.

Anoop
FEBRUARY 14, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post How to Install SCCM Client using Intune for Autopilot Provisioned Devices appeared first on HTMD Blog #1 by Kannan CS.

Tech Republic Security
FEBRUARY 24, 2022
Whether the chicken or the egg came first, Beyond Identity’s data suggests that the fastest growing companies are all more likely to take cybersecurity seriously. The post What hyper-growth companies all have in common: They prioritize cybersecurity appeared first on TechRepublic.

Network World
FEBRUARY 14, 2022
Power, they say, corrupts, and absolute power corrupts absolutely. While that was said about politics, it sure seems like it was tailor-made for smart buildings. Facility-control technology is exploding because the concept is useful and often saves money. Unfortunately, smart devices have also proven to be an on-ramp for major intrusions. Smart buildings are surely absolutely powerful in a way; are they absolutely corruptible?

Speaker: Christophe Louvion, Chief Product & Technology Officer of NRC Health and Tony Karrer, CTO at Aggregage
Christophe Louvion, Chief Product & Technology Officer of NRC Health, is here to take us through how he guided his company's recent experience of getting from concept to launch and sales of products within 90 days. In this exclusive webinar, Christophe will cover key aspects of his journey, including: LLM Development & Quick Wins 🤖 Understand how LLMs differ from traditional software, identifying opportunities for rapid development and deployment.

TechSpot
FEBRUARY 3, 2022
Microsoft CEO Satya Nadella recently held an interview with Financial Times (reprinted by Ars Technica), wherein he laid out the potential for the metaverse and its similarities with games. He went so far as to say the two are essentially the same thing.

Information Week
FEBRUARY 22, 2022
The answer for IT and business leaders facing exodus: Focus on product-led growth to limit the impact of talent departure and team productivity.

Gizmodo
FEBRUARY 8, 2022
Science fiction cinema would not be what it is today without the work of Douglas Trumbull. Trumbull helped drive effects on films like 2 001: A Space Odyssey , Blade Runner , and Close Encounters of the Third Kind , each time changing the field in ways that would resonate for decades. After an incredible life and career,… Read more.
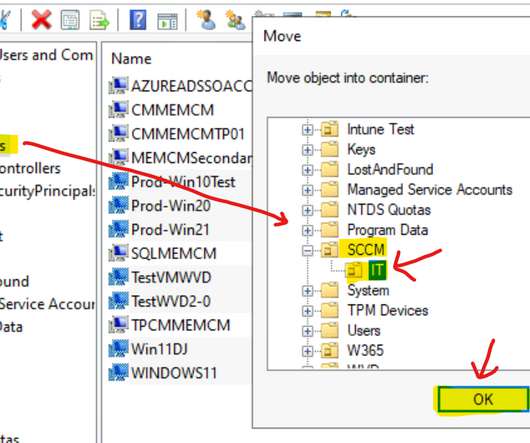
Anoop
FEBRUARY 21, 2022
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link]. and Facebook Page to get the latest updates. [link]. Read More. The post SCCM Collection based on Active Directory OU | The Easy Way appeared first on HTMD Blog #1 by Anoop C Nair.
Advertisement
There’s no getting around it: selecting the right foundational data-layer components is crucial for long-term application success. That’s why we developed this white paper to give you insights into four key open-source technologies – Apache Cassandra®, Apache Kafka®, Apache Spark™, and OpenSearch® – and how to leverage them for lasting success. Discover everything you’ll want to know about scalable, data-layer technologies: Learn when to choose these technologies and when to avoid them Explore h

Tech Republic Security
FEBRUARY 22, 2022
2021 saw a decrease in mobile malware attacks, yet they have become increasingly sophisticated. Learn more about these threats and how to avoid being a victim. The post 2021 mobile malware evolution: Fewer attacks, escalating dangers appeared first on TechRepublic.
Network World
FEBRUARY 23, 2022
Zero trust touches everything: identity, applications, networks, data, and devices. The best approach is not to change everything all at once. Instead, start with the big picture. In our research, we’ve found the most successful organizations dedicated the first phase of their zero-trust initiatives to working out an architecture. They didn’t rush into deploying solutions as though starting with a greenfield.

TechSpot
FEBRUARY 23, 2022
ICQ, short for the phrase "I Seek You," laid the groundwork for standalone instant messaging clients when it arrived in November 1996. Think about how long ago that was. Windows 95 was barely a year old, Nintendo had just introduced the N64, and those with a reason to have a.

Information Week
FEBRUARY 11, 2022
Automation is helping accelerate business processes and organizations. For those looking to land a job in IT automation, a long list of IT skills can be applied.

Advertisement
IT leaders are experiencing rapid evolution in AI amid sustained investment uncertainty. As AI evolves, enhanced cybersecurity and hiring challenges grow. This whitepaper offers real strategies to manage risks and position your organization for success.
Let's personalize your content