AI and The End Of Software Development As We Know it.
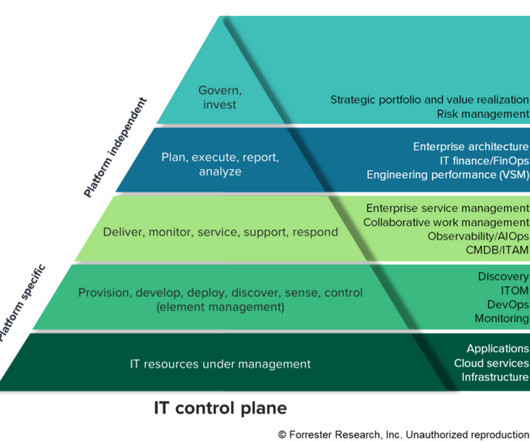
Forrester IT
JULY 31, 2024
We’ve tried Agile, DevSecOps and LowCode, Now What? Past and future technologies and paradigms shifts like Agile, DevOps, low-code, and even AI have been reshaping the software development world. Now, generative AI is disrupting it. The software development lifecycle (SDLC), is being accelerated and reimagined as a process happening in real-time.










































Let's personalize your content