Ransomware attackers are now using triple extortion tactics
Tech Republic Security
MAY 12, 2021
Attackers are not only demanding ransom from organizations, but also threatening their customers, users and other third parties.
Tech Republic Security
MAY 12, 2021
Attackers are not only demanding ransom from organizations, but also threatening their customers, users and other third parties.

Information Week
MAY 13, 2021
Not everyone has been trained to think like a data scientist or a data analyst, but they can learn to think more like one.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Forrester IT
MAY 10, 2021
I spent the early days of my career in the early 90’s studying manufacturing engineering at University then working in a ship repair yard. I was taught to weld by a gruff Geordie who handed me a visor, a live arc-welder and told me “don’t look into the light. You’ll go blind”. I didn’t. That […].

CTOvision
MAY 12, 2021
Security can be enhanced and major risks mitigated by realistic threat emulation. This is needed now more than ever. Professionals in the security community except it as a given that we should all raise defenses, but prepare for breach. Raising defenses means checking for gaps so appropriate controls can be applied. And preparing for breach […].

Advertiser: ZoomInfo
Sales and marketing leaders have reached a tipping point when it comes to using intent data — and they’re not looking back. More than half of all B2B marketers are already using intent data to increase sales, and Gartner predicts this figure will grow to 70 percent. The reason is clear: intent can provide you with massive amounts of data that reveal sales opportunities earlier than ever before.

Association of Information Technology Professional
MAY 12, 2021
Ready to grow your cloud computing career or get it off to a great start? If so, check out the best cloud computing certifications today.
Social, Agile and Transformation
MAY 10, 2021
I have to admit that I'm skeptical whether non-technical companies will successfully execute a software development strategy routed in microservices. There's a long history of software development teams seeking modular and reusable code and services. We chased object-oriented programing, generic methods, and service-oriented architectures, leaving a trail of.
Information Technology Zone brings together the best content for IT professionals from the widest variety of industry thought leaders.

CTOvision
MAY 12, 2021
Read Alex Woodie explain how Aerospike is pushing Spark machine learning training with pushdown processing on Datanami : Companies that need to access a lot of data in a hurry, such as retraining a machine learning model in Spark, have traditionally had to move that data from the edge to a central repository, such as […].

Association of Information Technology Professional
MAY 10, 2021
How can you enhance protections for remote workers and support their activities? For many businesses, the solution is coming in the form of SD-WAN.

The Accidental Successful CIO
MAY 12, 2021
CIOs need to understand how to make use of new business intelligence tools Image Credit: deepak pal. Modern CIOs need to understand that Business intelligence (BI) leverages software and services to transform data into actionable insights that inform an company’s strategic and tactical business decisions. These BI tools access and analyze data sets and present analytical findings in reports, summaries, dashboards, graphs, charts and maps designed to provide users with detailed intelligence

Forrester IT
MAY 13, 2021
This may be a bit of a long blog due to the extensive nature of the Executive Order On Improving The Nation’s Cybersecurity and its impact on cybersecurity and the Zero Trust approach. The Biden administration also published a “FACT SHEET: President Signs Executive Order Charting New Course to Improve the Nation’s Cybersecurity and Protect […].

Advertiser: GEP
For years, you and your team have fought an uphill battle. Supply disruptions. Cost pressures. ESG compliance. You name it, and you’ve had to navigate it. In 2025, many challenges will persist, but procurement and supply chain teams have a powerful tool with rapidly advancing capabilities to tackle them — artificial intelligence (AI). The GEP Outlook 2025 report examines the disruptive transformation AI is driving in procurement and supply chains, alongside other key trends and the macroeconomic

CTOvision
MAY 12, 2021
The price of Ether surged past $3,000 on May 4 making its creator, Vitalik Buterin, the world’s youngest crypto billionaire at the age of 27. Cryptocurrency ether extended gains to another record peak, after breaking above $3,000 for the first time a day earlier as investors bet on its growing utility. Early in Asia trade it […].

Anoop
MAY 13, 2021
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Read More. The post How to Improve SCCM Task Sequence Progress Bar End User Experience | ConfigMgr appeared first on HTMD Blog by Jitesh Kumar.

Tech Republic Data Center
MAY 11, 2021
A recent report on DC power revealed some interesting trends related to data center operations and power. Learn what data center conditions look like today and going forward.
Forrester IT
MAY 10, 2021
Many companies get emotion wrong… Rather than designing experiences built on a broad spectrum of emotions, they equate emotion with delight. But real joy and real happiness can only exist in relation to all the emotions, they are a “boxed set.” We cannot just pick and choose our emotions. Anger isn’t joy, just as joy […].

Speaker: Carolyn Clark and Miriam Connaughton
Forget predictions, let’s focus on priorities for the year and explore how to supercharge your employee experience. Join Miriam Connaughton and Carolyn Clark as they discuss key HR trends for 2025—and how to turn them into actionable strategies for your organization. In this dynamic webinar, our esteemed speakers will share expert insights and practical tips to help your employee experience adapt and thrive.

CTOvision
MAY 12, 2021
Read Mark Wright explains how converging technologies are driving up usage of Elasticsearch on EE Times. Digital convergence is happening all around us as technologies that were originally unrelated come together in exciting new ways. The iPhone is a perfect example, combining a phone with a computer, a camera and sensors to deliver an outstanding […].

Anoop
MAY 12, 2021
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Read More. The post Easy Steps to Run SCCM Task Sequence with High Performance Power Plan | ConfigMgr appeared first on HTMD Blog by Jitesh Kumar.

Tech Republic Security
MAY 12, 2021
Government and business both need to step up to combat ransomware attacks against critical systems before they spiral further out of control.

Forrester IT
MAY 12, 2021
Our society is coping with unprecedented challenges. Your customers, employees, and partners are all facing growing uncertainties and concerns, such as: income inequality and job insecurity, social unrest, and misinformation and disinformation. Meanwhile, systemic risks like climate change, pandemics, and global recessions have wrought significant health, safety, and financial impacts.

Advertisement
Large enterprises face unique challenges in optimizing their Business Intelligence (BI) output due to the sheer scale and complexity of their operations. Unlike smaller organizations, where basic BI features and simple dashboards might suffice, enterprises must manage vast amounts of data from diverse sources. What are the top modern BI use cases for enterprise businesses to help you get a leg up on the competition?

CTOvision
MAY 12, 2021
A DeFi platform says its decentralized approach to leveraged trading offers crucial advantages over centralized rivals. Gains.farm says it offers real-time prices and lightning-fast transactions — and boasts a network of five Chainlink nodes that delivers up-to-date information from seven trusted data sources, with results that are aggregated by taking the median two times.

Information Week
MAY 10, 2021
The cloud is set to help businesses lead by outmaneuvering uncertainty. It's now imperative that they lean into the cloud and catch up with leaders before the gap becomes too large.

Tech Republic Security
MAY 11, 2021
Cybersecurity expert discusses the many ways attackers could have gotten access to the Colonial Pipeline company and reminds us why the threat always looms.

Forrester IT
MAY 10, 2021
While automated malware analysis and network intrusion detection systems remained in our Divest category, three more technologies joined them this year: data loss prevention, managed security service providers, and security user behavior analytics. Why is this? Because these stand-alone technologies simply don’t cut it anymore. This isn’t to say these solutions are dead, mind you.

Advertiser: ZoomInfo
In this exploration, we're diving into predictions about the future of sales. We're talking about a complete shake-up powered by automation and artificial intelligence (AI). These aren't just fancy tools — they're real game-changers. Automation and AI are here to redefine every interaction, making them smarter, faster, and more meaningful. From personalized customer journeys to streamlined sales processes, the goal is to make every moment count, enhancing both efficiency and connection.

CTOvision
MAY 12, 2021
Critics of IBM say the American tech icon went the hybrid cloud way because it lost the fight to become a public cloud hyper-scaler to Amazon Web Services and Microsoft. Hybrid clouds are a combination of privately-owned computer servers and networks and machines and services rented off the internet. Public ones, on the other hand, […].

Information Week
MAY 12, 2021
The C-suite has expanded, but will the trend continue? Likely yes, but how depends on what your company values most.

Tech Republic Security
MAY 10, 2021
A recent survey found an unusual reason cybersecurity is failing. Experts share what it is and how to correct it.

Forrester IT
MAY 10, 2021
New data from the UK Office Of National Statistics (ONS) shows that one in five adults in Britain experienced depressive symptoms in early 2021, more than double the proportion before the pandemic. Young adults are coping with a significant increase of mental health issues. Financial concerns, managing children in the household, and disabilities are some […].

Advertiser: Procom Services
Procom’s 2024 Salary Guide provides critical insights into the latest hiring trends, in-demand IT roles, and competitive pay rates across Canada and the U.S. It highlights key market dynamics such as the growing demand for remote work, skills-based hiring, and flexible staffing solutions. With detailed pay rate data for top IT positions like Cybersecurity Consultants, Cloud Engineers, and Salesforce Developers, this guide is an essential resource for companies looking to stay competitive in toda

CTOvision
MAY 12, 2021
There’s a good chance Dogecoin (CRYPTO: DOGE) is going to be around for a while, Palantir Technologies Inc (NYSE:PLTR) co-founder Joe Lonsdale said Thursday on CNBC’s “Squawk Box.” If Elon Musk, CEO of Tesla Inc (NASDAQ:TSLA) and SpaceX, decides he wants to make Dogecoin a currency on Mars, “I bet you he could do it,” Lonsdale […].

Information Week
MAY 14, 2021
Though challenges arise when implementing a strategy to capitalize on data currency, the rewards are worth the effort. Here are six ways to unlock the value of your data.

Tech Republic Security
MAY 10, 2021
Diving into a cashless future of transactions via digital wallets that keep consumers safe and reduce paper and waste.

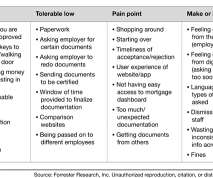
Forrester IT
MAY 12, 2021
Improving reps' productivity is one of the top objectives of our sales leader clients. The first step to achieving this is to truly understand the key productivity obstacles today’s sales teams face.

Advertisement
For many IT admins, business as usual is a juggling act. Job schedulers and scripts run on autopilot, applications and operating systems can’t speak the same language, and other tools—like RPA or MFT solutions—operate in isolation. On a good day, everything runs smoothly. But good days are rare; more often than not, something goes wrong and you’re stuck putting out fires.
Let's personalize your content