KubeCon + CloudNativeCon Highlights Security for Open Source
Information Week
OCTOBER 15, 2021
Vulnerabilities in the life cycle of open-source software development can start from tiny crumbs but grow into substantial issues.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Information Week
OCTOBER 15, 2021
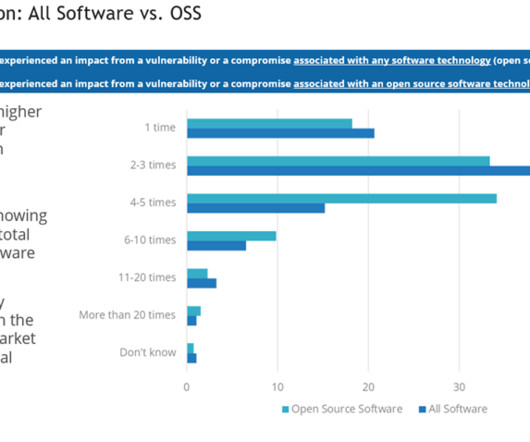
Vulnerabilities in the life cycle of open-source software development can start from tiny crumbs but grow into substantial issues.

CIO Business Intelligence
MARCH 25, 2025
Accenture reports that the top three sources of technical debt are enterprise applications, AI, and enterprise architecture. These areas are considerable issues, but what about data, security, culture, and addressing areas where past shortcuts are fast becoming todays liabilities?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Network World
JANUARY 30, 2025
When AI agents begin to proliferate, a new, open structure will be needed so they can securely communicate and collaborate together to solve complex problems, suggests Cisco. Infrastructure agents from Cisco and Microsoft simultaneously validate security, identity and access, costs, and SLO compliance.
CIO Business Intelligence
AUGUST 8, 2024
For many stakeholders, there is plenty to love about open source software. Developers tend to enjoy the ability to speed application development by borrowing open source code. CFOs like the fact that open source is often free or low in cost.

Tech Republic Security
DECEMBER 21, 2022
Microsoft has open sourced its framework for managing open source in software development. The post What is Microsoft’s Secure Supply Chain Consumption Framework, and why should I use it? appeared first on TechRepublic.

CIO Business Intelligence
NOVEMBER 20, 2024
From the start, Meta has made the Llama models available to other enterprises under a license it describes as “open source,” but the creation of the new business group makes clear that Meta’s interest is commercial, not philanthropic. Keeping control However, anyone wanting to use the latest Llama 3.2

CIO Business Intelligence
MAY 15, 2024
Even if you don’t have the training data or programming chops, you can take your favorite open source model, tweak it, and release it under a new name. According to Stanford’s AI Index Report, released in April, 149 foundation models were released in 2023, two-thirds of them open source.

CIO Business Intelligence
MARCH 19, 2025
Software development and IT Cognition released Devin, billed as the worlds first AI software engineer, in March last year. But there are already some jobs specifically in the software development lifecycle poised to be aided by AI agents. We cant do that for security reasons, he says.

Network World
NOVEMBER 5, 2024
VMware Tanzu RabbitMQ: “Secure, real-time message queuing, routing, and streaming for distributed systems, supporting microservices and event-driven architectures.” VMware Tanzu for MySQL: “The classic web application backend that optimizes transactional data handling for cloud native environments.” I would have to say yes.” Not at all.”

Network World
JUNE 17, 2024
Linux is very well known and appreciated in the automotive industry with increasing attention being paid both to its reliability and its security. Why open source? Open source places a huge role in the automotive use of Linux. In fact, even the car you’re driving today could be using Linux in some capacity.

CIO Business Intelligence
DECEMBER 10, 2024
Python Python is a programming language used in several fields, including data analysis, web development, software programming, scientific computing, and for building AI and machine learning models. Kubernetes Kubernetes is an open-source automation tool that helps companies deploy, scale, and manage containerized applications.

CIO Business Intelligence
JULY 18, 2024
Despite the importance of the mainframe, it has been neglected over the years with organizations focusing on perimeter security. According to Gartner , IT security software is the top purchase category (28%) for those buying IT-related software. But only eight percent of those buyers are purchasing IT management software.

CIO Business Intelligence
NOVEMBER 13, 2023
No matter the industry, organizations are increasingly looking for ways to optimize mission-critical software development processes. As development teams grapple with the challenge of modernizing their DevOps toolchains, a number of concerns and challenges have followed closely behind. Chief among those challenges?

Tech Republic Security
DECEMBER 20, 2022
Open source software development service has made it easier for developers using its public repositories to keep coding secrets and tokens close to the chest. The post GitHub offers secret scanning for free appeared first on TechRepublic.

CTOvision
AUGUST 20, 2020
explain how you can stay secure on GitHub on Dark Reading : Open source software is a fact of life for enterprise software developers, and GitHub […]. Read Curtis Franklin Jr.

CIO Business Intelligence
DECEMBER 20, 2024
Ensure security and access controls. Modern data architectures must be designed for security, and they must support data policies and access controls directly on the raw data, not in a web of downstream data stores and applications. The Open Group Architecture Framework. Container orchestration. Real-time analytics.

CTOvision
NOVEMBER 12, 2014
Dealing with the scale that the internet can deliver, has unfortunately left us with a series of other non-optimal cyber security approaches and solutions. Out of all the problems to deal with subverting bureaucracy to enable security scaling is the hardest. In cybersecurity we’re have a hard time dealing with scale.
CIO Business Intelligence
APRIL 24, 2024
The complexity of the software supply chain (SSC) has the potential to expose your organization to greater risk than ever before. In today’s fast-paced software development landscape, managing and securing the software supply chain is crucial for delivering reliable and trusted software releases.

Network World
MARCH 3, 2017
HackerOne, the company behind one of the most popular vulnerability coordination and bug bounty platforms, has decided to make its professional service available to open-source projects for free. Here at HackerOne, open source runs through our veins," the company's representatives said in a blog post.

Network World
JULY 11, 2016
Companies that develop enterprise applications download over 200,000 open-source components on average every year and one in every 16 of those components has security vulnerabilities.

CIO Business Intelligence
MARCH 12, 2025
This is simply because each cloud platform works with its own management tools, security protocols and performance metrics. The open-source system is available in practically every public cloud, and most local cloud providers also offer Kubernetes. Security is one of the main issues.
CIO Business Intelligence
JUNE 20, 2023
As such, it’s vital to have a robust and forward-leaning approach to web application security. With an estimated market size of USD $30B by 2030 , the term “application security” takes on numerous forms, but one area of heightened relevance in today’s world is the DevSecOps space. What is DevSecOps?

CIO Business Intelligence
MARCH 9, 2023
It’s completely intuitive, allows me to perform most tasks in less than 3 clicks, has all the functions that I need to perform banking on-the-go, is constantly updated with new features, comes with great performance and stability and most of all is very secure. Today its offerings include deliveries, mobility, financial services among others.

Venture Beat
JANUARY 24, 2021
Russia's SolarWinds hack gave it access to data from federal agencies because we haven't secured the software supply chain. Read More.

CIO Business Intelligence
JULY 13, 2022
Shadare, along with Orca Security advisory CISO Andy Ellis and Spire Security Vice President of Research Pete Lindstrom, will share cybersecurity metrics that matter as part of CSO’s Future of Cybersecurity Summit , taking place virtually July 19-20. One risk mitigation strategy is to move away from passwords to more secure protocols.

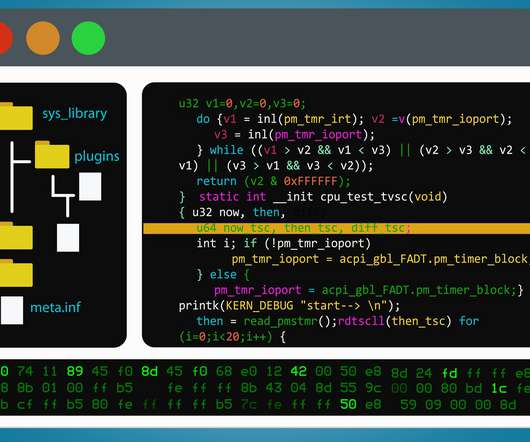
Venture Beat
OCTOBER 20, 2021
ControlFlag, an AI-powered tool developed by Intel to spot potential issues in software code, has been released in open source. Read More.

CTOvision
NOVEMBER 21, 2014
This webinar will examine how to economically enhance security and functionality by leveraging Cloudera and Intel. Enhance security. Previously, Webster held positions in sales and services at companies like Microsoft and FAST Search and Transfer and in software development at firms like Time Inc.

CIO Business Intelligence
MAY 1, 2023
Software agility also means that if the organization would like to leverage a new technology to innovate and remain competitive, teams can easily deliver an app that does just that. This will help in optimizing application development and operations, and strengthening security and compliance. Software Development
Venture Beat
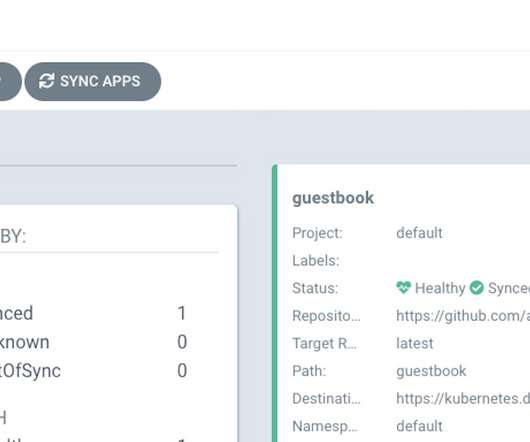
FEBRUARY 3, 2022
A zero day vulnerability with a "high" severity rating affects Argo CD, an open source developer tool for Kubernetes, Apiiro researchers said. Read More.

CTOvision
DECEMBER 5, 2014
This webinar will examine how to economically enhance security and functionality by leveraging Cloudera and Intel. Enhance security. Previously, Webster held positions in sales and services at companies like Microsoft and FAST Search and Transfer and in software development at firms like Time Inc.

CIO Business Intelligence
SEPTEMBER 14, 2022
Demand has increased so much that IT job postings in manufacturing doubled between May 2021 and 2022, according to Dice.com, with increased demand for skills such as agile development, Python, software development, automation, C++, SQL, and Java, among others. Software developer. DevSecOps engineer.

IT Toolbox
AUGUST 17, 2022
Smart firms maintain an up-to-date, credible SBOM for their projects that includes a list of all the open source and third-party components that are used to create high-quality, ethical, and secure code. This article discusses SBOM in greater detail.

CIO Business Intelligence
AUGUST 9, 2024
If there’s flexibility in the timeline, creating a custom solution can provide greater value.But the skills required to develop in-house generative AI tools are specialized and in high demand, so getting the right people on board is a must. Safety and Security As generative AI becomes more encompassing, it must be used safely and responsibly.

CIO Business Intelligence
OCTOBER 1, 2024
This necessitates continuous adaptation and innovation across various verticals, from data management and cybersecurity to software development and user experience design. Let’s talk about strengthening the four major pillars from an attacker’s perspective, as they form the core of any organization’s security.
Venture Beat
MAY 4, 2022
Appwrite has launched a dedicated fund to support open source project maintainers, following shortly after its recent $27 million fundraise. Read More.

CIO Business Intelligence
OCTOBER 27, 2023
The courses are designed to be completed in succession, starting with the Apple Device Support course, which focuses on the skills and expertise you’ll need as a help desk professional, technical coordinator, or service provider for an organization that relies on Apple hardware and software.

CIO Business Intelligence
JUNE 9, 2022
Not only are organizations struggling to attract and retain technical talent in today’s competitive market, but the number of developers who understand code on mainframe systems is limited. DevSecOps, which is different from DevOps in that it integrates security as a shared responsibility throughout the entire IT lifecycle.

CIO Business Intelligence
DECEMBER 20, 2023
But as the adoption of DevOps grew in organizations, so did the complexity of the world they live in: from highly powerful but complex cloud infrastructure to increasingly sophisticated security attacks, and constantly evolving and cumulative compliance requirements. to developers. Devops, Software Development

CIO Business Intelligence
JULY 10, 2024
The final stage of responsible AI are the AI guardrails, and organizations can deploy the ones that come with their AI platforms, use third-party vendors and startups, or build guardrails from scratch, typically with the help of open-source components. Tines ensures the security of MyFitnessPal’s data, Talaga says.

CIO Business Intelligence
MARCH 4, 2025
These select choices can then be of high quality, well-supported, documented, maintained, secure, and reliable. Another golden path is reducing time spent on information search and discovery, which Block estimates could save up to another 200,000 hours of developer time annually. For example, most recently we built an AI migrator tool.

CTOvision
DECEMBER 21, 2013
Tom has a distinguished 30-year career in the enterprise software market. Prior to Cloudera, his most recent role was as vice president and general manager of enterprise security at HP. Previous to HP, Tom served as CEO of enterprise security company ArcSight , which HP acquired in 2010. in Electrical and Computer Engineering.

CTOvision
SEPTEMBER 8, 2014
SECURITY & COMPLIANCE. Operating Hadoop as a controlled, mission-critical environment that meets stringent mandates for security and regulatory compliance. Tony Baer has a multi-disciplinary background touching the different tiers of enterprise software. GOVERNMENT, NONPROFIT, & NGO. Research VP, Gartner.

CIO Business Intelligence
APRIL 17, 2024
Helping software developers write and test code Similarly in tech, companies are currently open about some of their use cases, but protective of others. So far, Castillo has been publishing her work with open-source licenses. And unit tests are too tedious for humans to build reliably.

CIO Business Intelligence
AUGUST 14, 2024
It’s embedded in the applications we use every day and the security model overall is pretty airtight. For many enterprises, Microsoft provides not just document and email storage, but also the root of enterprise identity for those data sources, as Vadim Vladimirskiy, CEO of software developer Nerdio, points out.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content